#FactCheck - AI-Generated Video Falsely Claims Israeli PM Netanyahu Announced Aid for Afghanistan at PM Modi’s Request
Executive Summary:
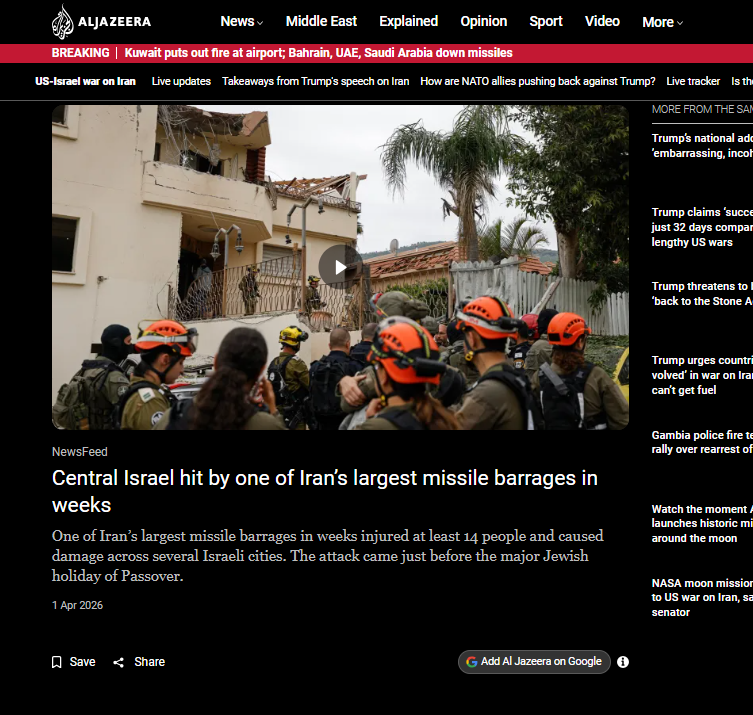
A video is widely circulating on social media in which Israel’s Prime Minister Benjamin Netanyahu appears to praise India’s Prime Minister Narendra Modi. The viral clip is being shared with the claim that during a speech delivered on February 25, 2026, Netanyahu announced a special aid package for Afghanistan at the request of PM Modi. However, research by CyberPeace found the claim to be false. The research revealed that the circulating video was generated using artificial intelligence. The probe also confirmed that Netanyahu did not make any announcement related to Afghanistan or the Taliban during the speech.
Claim
On March 1, 2026, a social media user shared the viral video on Facebook claiming that Netanyahu praised PM Modi and announced a special assistance package for Afghanistan following India’s request. The links to the post and its archive are provided below, along with a screenshot.

Fact Check:
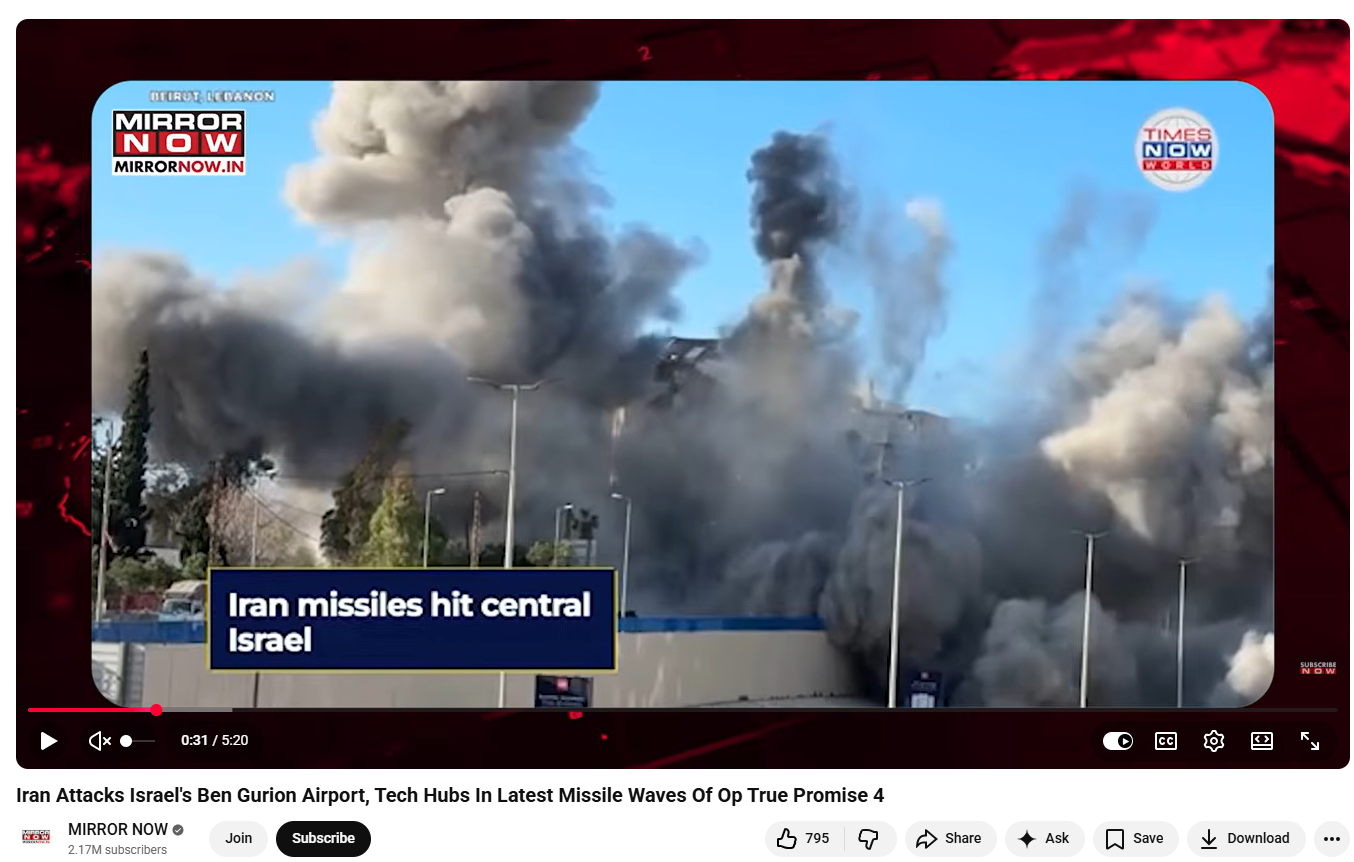
To verify the claim, we first searched Google using relevant keywords. However, we did not find any credible media reports supporting the claim that Israel had announced such an aid package for Afghanistan. Next, we extracted key frames from the viral video and performed a reverse image search using Google Lens. During this process, we found the original video on the YouTube channel of VERTEX, which had been uploaded on February 25, 2026.
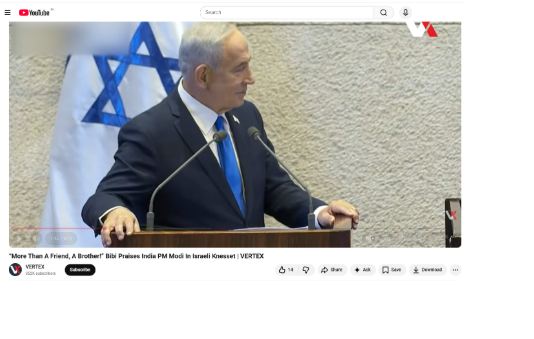
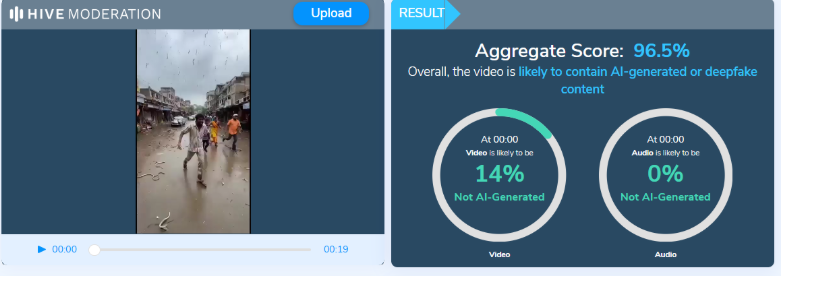
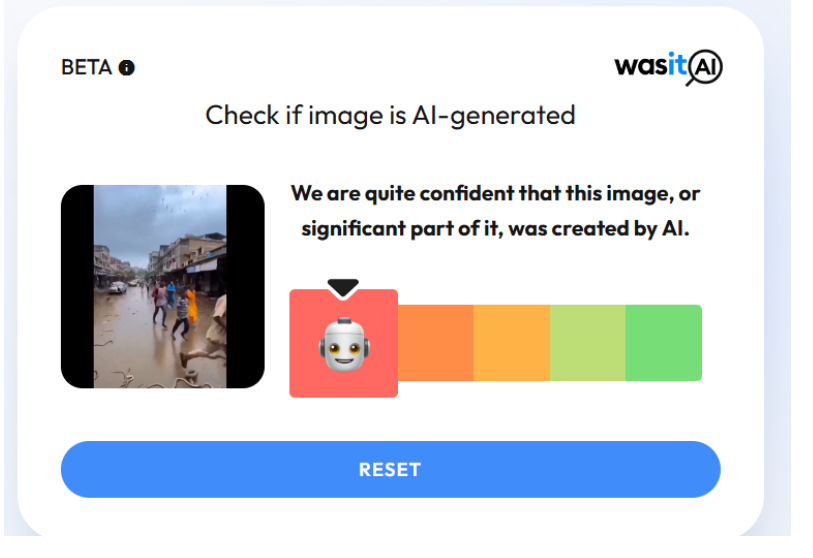
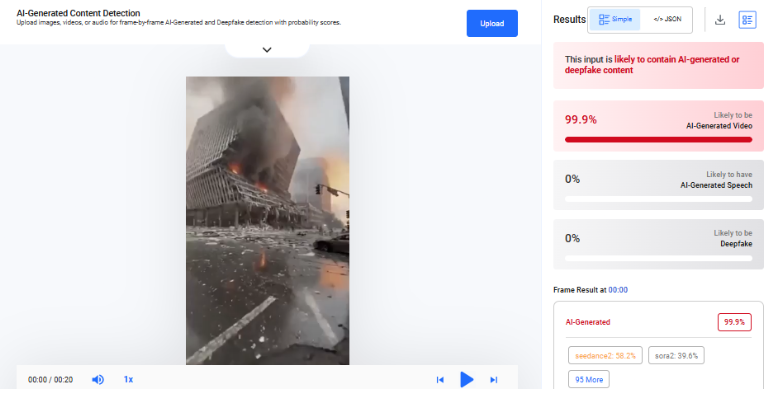
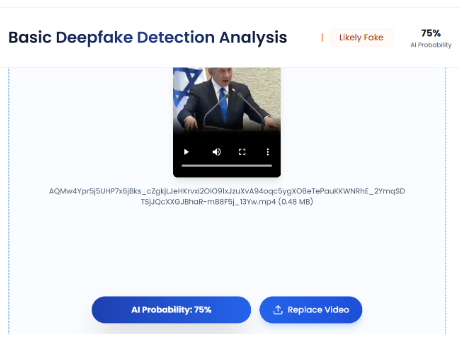
A detailed review of the original video revealed that the viral clip circulating on social media is not part of the original footage. This indicates that the circulating clip has been manipulated and shared with a misleading claim. In the original video, Netanyahu was addressing a special parliamentary session in Jerusalem, where he spoke about the growing trade, strategic cooperation, and strengthening diplomatic relations between India and Israel. He described the partnership between the two democracies as a significant and historic milestone in bilateral relations. Upon carefully listening to the viral clip, we noticed irregularities in the voice and tone, which raised suspicions that it might be AI-generated. We then analyzed the video using the AI detection tool TruthScan. The results indicated that the viral video has approximately a 75% probability of being AI-generated.
Conclusion
Our research found that the viral video was created using artificial intelligence. Moreover, Israel’s Prime Minister Benjamin Netanyahu did not make any announcement regarding Afghanistan or the Taliban during the speech being referenced. The claim circulating on social media is therefore false.