#FactCheck- Burning Helicopter Video Not From Iran, Dates Back to 2020 Syria
Executive Summary
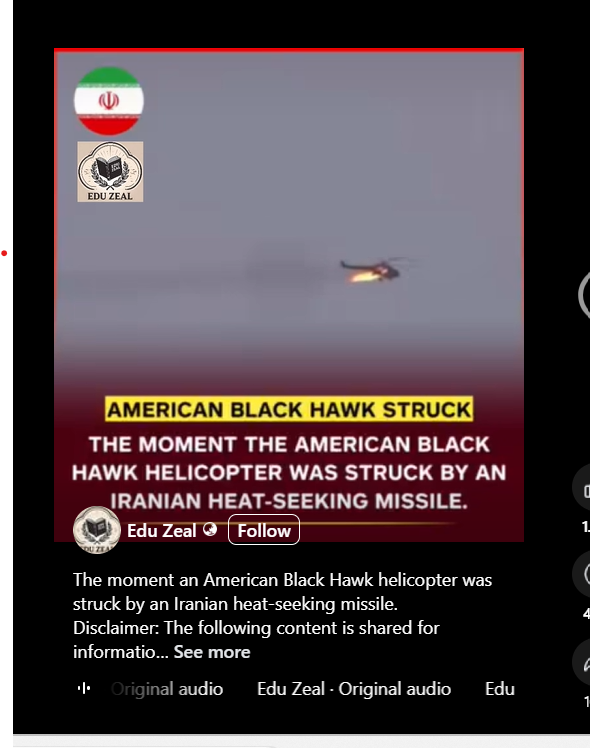
A video showing a helicopter engulfed in flames is being widely circulated on social media with the claim that it depicts an American Black Hawk helicopter shot down by Iran during the ongoing Middle East conflict. However, research by the CyberPeace Research Wing found the claim to be false. The viral footage is old and dates back to February 2020, showing a helicopter shot down in Syria, not Iran.
Claim
A Facebook post shared from Nigeria on April 6, 2026, claimed: “The moment an American Black Hawk helicopter was struck by an Iranian heat-seeking missile.” The post, which has been shared over 100 times, includes a 50-second video showing a helicopter exploding mid-air and crashing to the ground.
Fact Check
On April 3, a US F-15E Strike Eagle was reportedly shot down over Iran, marking the first such incident since the start of the ongoing Middle East conflict.

Two Black Hawk helicopter deployed for a search-and-rescue mission for the jet’s crew were also hit by Iranian fire but managed to return to base, despite some crew members being injured.
- http://abcnews.com/Politics/us-fighter-jet-iran-search-rescue-officials/story?id=131685787&utm_source=chatgpt.com
US President Donald Trump had earlier announced the recovery of a missing pilot, describing it as “one of the most daring search and rescue operations in US history.
”
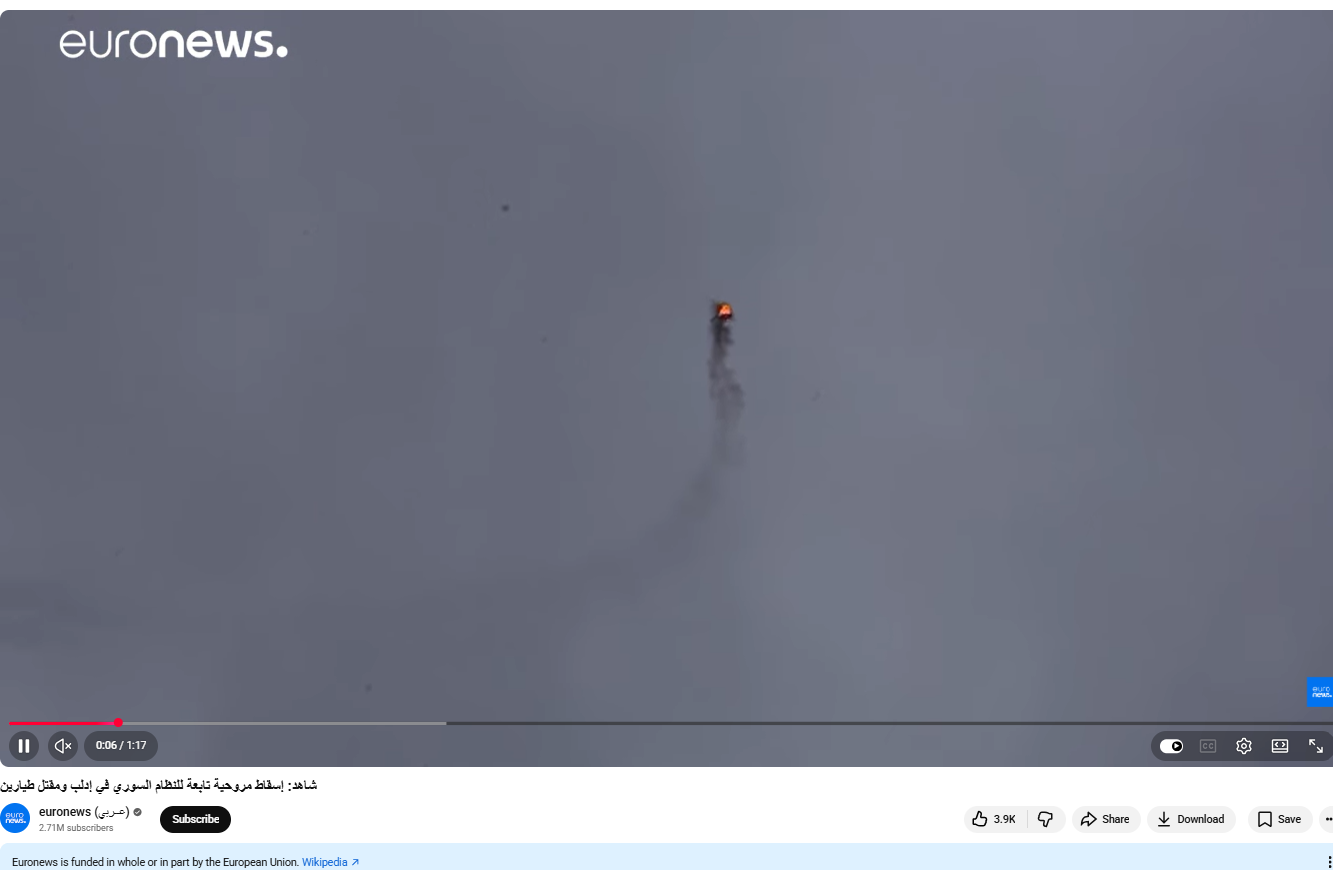
However, the viral video being shared as evidence of the downing of a US aircraft predates these events. Using reverse image search on keyframes from the clip, we found a longer version published by Euronews on February 11, 2020. The Arabic title of the video translates to: “Syrian regime helicopter shot down in Idlib, two pilots killed.” Reports indicate that the incident occurred in Idlib, Syria, in February 2020, where a military helicopter was shot down and caught fire before crashing.
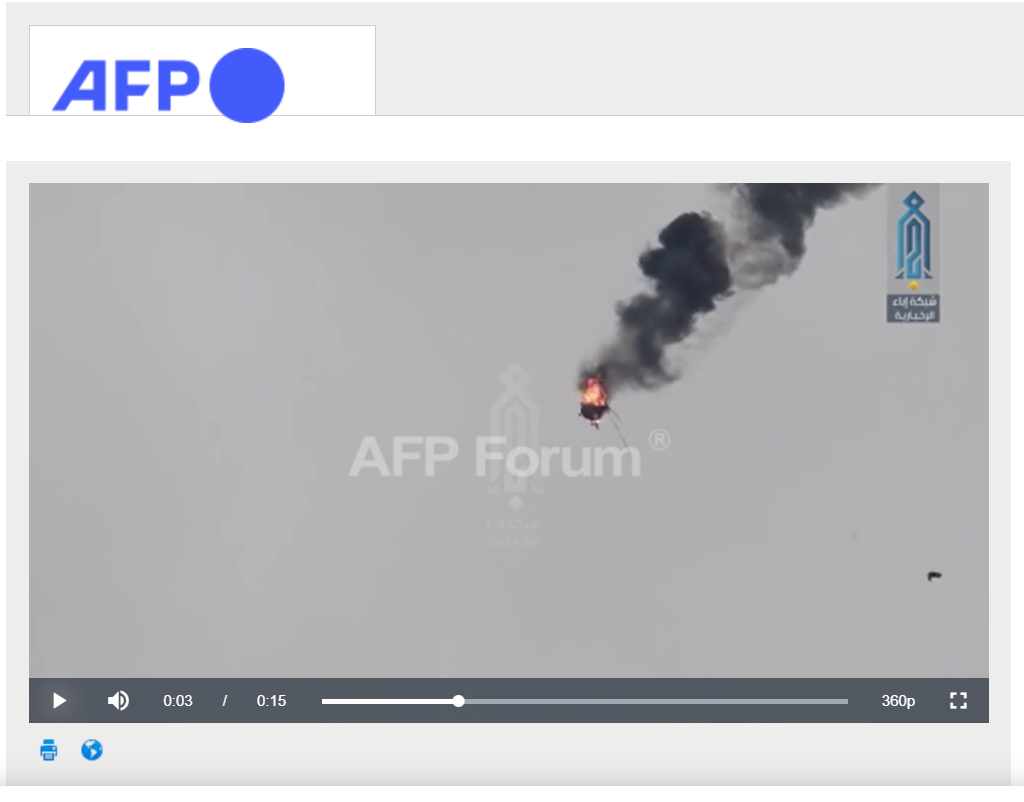
The incident was also covered by other international media outlets, including AFP, which distributed images and videos of the crash.
- https://www.afpforum.com/AFPForum/Search/ViewMedia.aspx?mui=1&hid=5DFA75509C25E3CDC3F24CA3B41C1A9A854C8AA3EB2BC1C64FCC0192F0506138
Conclusion
The viral claim is false. The footage does not show an American helicopter shot down by Iran. Instead, it is an old video from February 2020 depicting a helicopter crash in Syria, which is being shared with a misleading and unrelated narrative.