Introduction
In this age, when our data stands as the key to all resources, espionage has moved from dark alleys and trench coats to keyboards and code. In this era of active digital espionage, where intelligence is stolen through invisible cyberattacks that target computer networks. Cyber espionage and spying have become the most critical threat in the hyper-connected world of today. As governments, corporations, and individuals store an immense amount of confidential information online, the grounds of espionage have shifted from land and sea to the silent realm of cyberspace.
What is Cyber Espionage?
Cyber espionage refers to the unauthorised access of confidential data for strategic, political, military, and financial gain, unlike cybercrime, which is mostly about money. Cyber espionage is about gaining information power. The very first documented case dates back to 1986-87, when a group of German hackers breached the US military establishment and the defence systems and sold that stolen data to the Soviets and the KGB. This was the beginning of a new era where classified intelligence could be gathered even without entering a building.
Cyber espionage is mostly carried out by trained espionage professionals, elite hackers, and corporate spies whose sole purpose is to target the government, research organisations, military establishments, and other critical infrastructures.
The Objective
The act of Cyber Espionage is being driven by three major objectives, such as;
- Stealing of Intellectual Property- Starting from information and data related to military establishments to pharmaceutical patents, stealing innovation is cheaper than funding R&D.
- Political and Diplomatic Advantage- As government networks are hacked to access state secrets, negotiation strategies, and classified communications.
- Military Intelligence- Cyber spies also work to steal data on weapons troop movements, defence systems, and war systems, often years before conflict breaks out.
In a world being shaped by digital power, information is not just about knowledge. Rather, it is all about ensuring dominance.
The arsenal of modern digital spies is more sophisticated, and most importantly, they are used covertly rather than the spy gadgets that are shown in spy movies. Some of the tactics resorted to by the cyber spies can be recognised as;
- Phishing Attacks through fake emails that lure victims to click on malicious links or sharing of passwords.
- Persisting Advanced Threats through long-term stealth attacks in a network for more than a month or a year.
- Malware and Spyware are invisible software that logs keystrokes, records screens, or steals files silently.
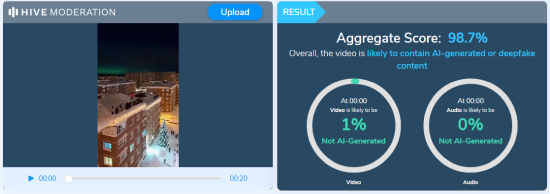
- Deepfake Manipulations by creating AI-generated fake videos that can influence political developments in the country.
Anything that makes cyber espionage terrifying is not just the theft, but the fact that it goes undetected.
What Differentiates Cyber Espionage and Cyber Warfare
Cyber espionage is a silent and stealthy tactic that is carried out with utmost secrecy, being a long-term effort for intelligence gathering. It mostly focuses on the stealing of data, whereas Cyber warfare is an open and destructive tactic that is used to create an immediate and visible impact to create disruption. However, espionage is an act that prepares the battlefield for the warfare of the future.
Taking instances of real instances of cyber espionage, we can refer to examples such as;
- Operation Aurora was conducted in 2010, where Chinese Hackers based in Beijing tried to steal IP data from Google and American tech giants.
- The Stuxnet attack in 2010 was another cyber weapon that was developed to sabotage Iran’s nuclear centrifuges.
- SolarWinds Attack of 2020 was an instance of cyber espionage where a supply chain hack was carried out to target multiple US federal government agencies.
As most of these instances reflect that they were battles without guns, but with the use of codes. Several sources raise the question of whether cyber-attacks can be stopped. The answer lies in the fact that they cannot be stopped completely, but can be minimised to some extent, by developing capabilities to counter and deter cyber-attacks with the help of equal cyber defence capabilities.
Conclusion
From the Cold War era to the present Code War, espionage has evolved with technology. An effort that was once taken solely by spies and human assets, with the passing of time enhancement of technologies it is now expanded to malware, phishing, social engineering, and remote digital inflation. In this age of information warfare, espionage is faster, cheaper, and harder to trace than ever before. The enemies of a nation may never cross its borders, but they may already be inside its systems. However, the world has now officially entered a new battlefield, without boundaries, uniforms, and bombs. It is now being fought through bytes, breaches, and invisible enemies.
References