#FactCheck -Viral Video of Electric Car Powered by Generator Is AI-Generated
Executive Summary
A video circulating on social media shows an electric car allegedly being powered by a portable generator attached to it. The clip is being shared with the claim that the generator is directly running the vehicle, suggesting a groundbreaking or unusual technological feat. However, research conducted by the CyberPeace found the viral claim to be false. Our research revealed that the video is not authentic but AI-generated.
Claim
On February 22, 2026, a user on X (formerly Twitter) shared the viral video with the caption: “After watching this video, Newton might turn in his grave.” The post implied that the video demonstrates a scientific impossibility.

Fact Check:
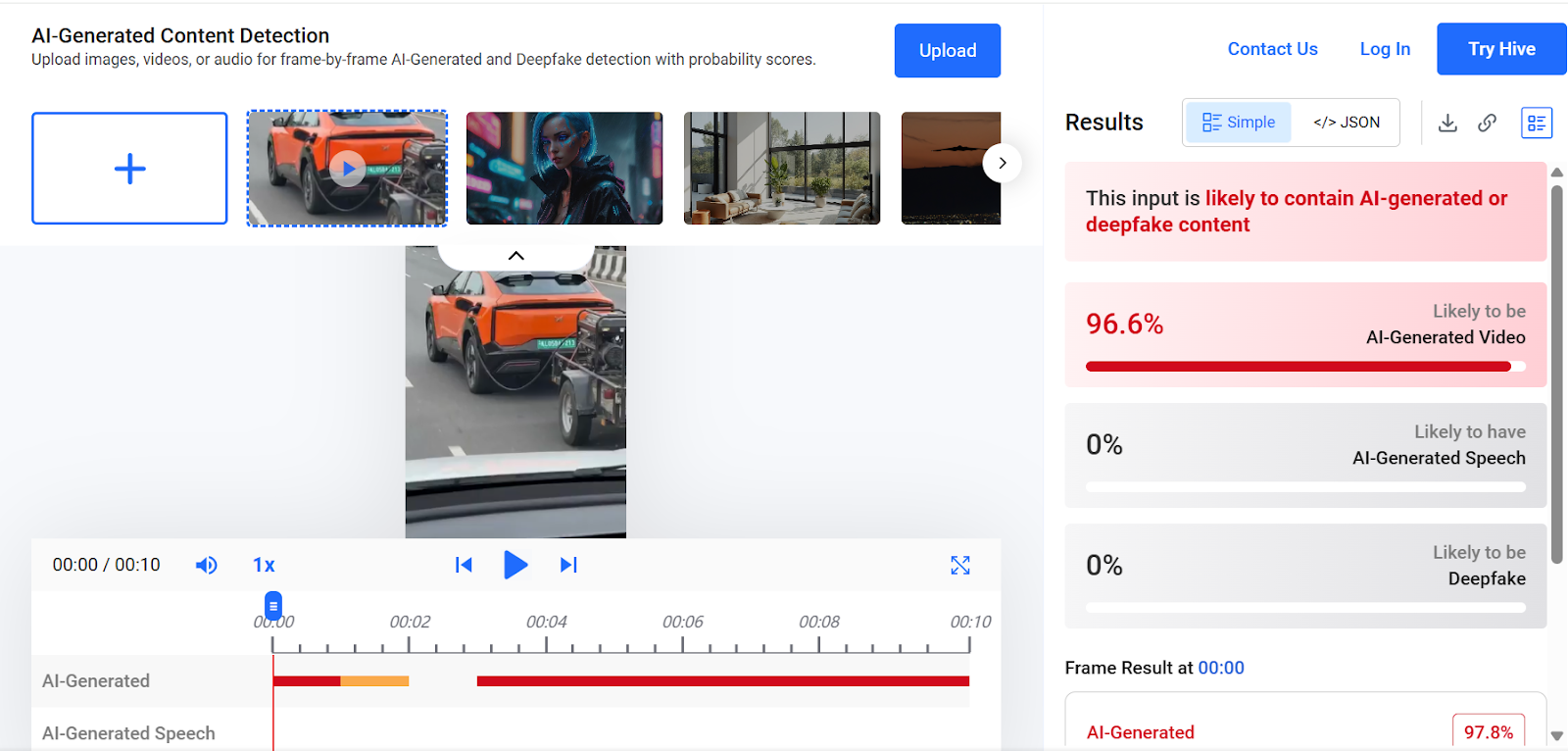
To verify the claim, we conducted a keyword search on Google. However, we found no credible reports from any reputable media organization supporting the assertion made in the viral post. A close examination of the video revealed several visual inconsistencies and unnatural elements, raising suspicion that the footage may have been generated using artificial intelligence. We then analyzed the video using the AI detection tool Hive Moderation. The results indicated a 96 percent probability that the video was AI-generated.
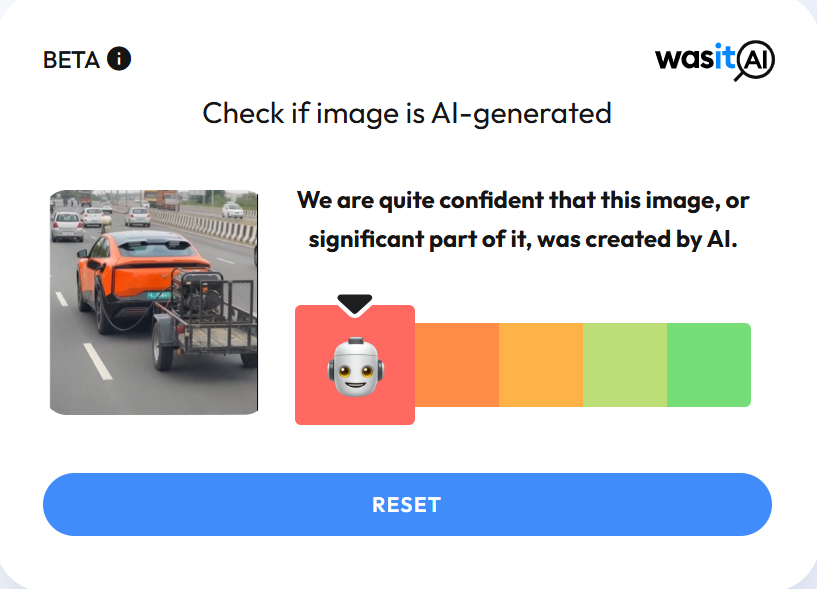
In the next step of our research , we scanned the video using another AI detection platform, WasItAI, which also concluded that the viral video was AI-generated.
Conclusion
Our research confirms that the viral video is not real. It has been artificially created using AI technology and is being circulated with a misleading claim.
Related Blogs
.webp)
Smart Wearable devices are designed to track several activities in defined parameters and are increasingly becoming a part of everyday life. According to Markets and Markets Report, the global wearable tech market is projected to reach a staggering USD 256.4 billion by 2026. One of the main areas of use of wearable devices is health, including biomedical research, health care, personal health practices and tracking, technology development, and engineering. These wearable devices often include digital health technologies such as consumer smartwatches that monitor an individual's heart rate and step count, and other body-worn sensors like those that continuously monitor blood glucose concentration.
Wearable devices used by the general population are getting increasingly popular. Health devices like fitness trackers and smartwatches enable continuous monitoring of personal health. Privacy is an emerging concern due to the real-time collection of sensitive data. Vulnerabilities due to unauthorised access or discrimination in case of information being revealed without consent are the primary concerns with these devices. While these concerns are present a lot of related misinformation is emerging due to the same.
While wearable devices typically come with terms of use that outline how data is collected and used, and there are regulations in place such as EU Law GDPR, such regulations largely govern the regulatory compliances on the handling of personal data, however, the implementation and compliances by the manufacturer is a one another aspect which might present the question on privacy protection. In addition, beyond the challenge of regulatory compliance, the rise of myths and misinformation surrounding wearable tech presents a separate issue.
Common Misconceptions About Privacy with Wearable Tech
- With the rapid development and growth of wearable technology their use has been subject to countless rumours which fuel misinformation narratives in the minds of general public. Addressing these misconceptions and privacy concerns requires targeted strategies.
- A prevalent misconception is that they are constantly spying on users. While wearable devices collect users’ data in real time, their vulnerability to unauthorised access is similar to that of a non-wearable device. The issue is of consent when it comes to wearable technology because it gives the ability to record. If permissions are not asked when a person is being recorded then the data is accessible to external entities.
- There is a common myth that wearable tech is surveillance tool. This is entirely a conjecture. These devices collect the user data with their prior consent and have been created to provide them with real-time information, most commonly physical health information. Since users choose the information shared, the idea of wearable tech serving as a surveillance tool is unfounded.
- Another misconception about wearable tech is that it can diagnose medical conditions. These devices collect real-time health data, such as heart rate or activity levels, they are not designed for medical diagnosis. The data collected may not always be accurate or reliable for clinical use to be interpreted by a healthcare professional. This is mainly because the makers of these devices are not held to the safety and liability standards that medical providers are.
- A prevalent misconception is that wearable tech can cure health issues, which is simply untrue. Wearable tech devices are essentially tracking the health parameters that a user sets. It in no way is a cure for any health issue that one suffers from. A user can manage their health based on the parameters they set on the device such as the number of steps that they walk, check on the heart rate and other metrics for their mental satisfaction but they are not a cure to treat diseases. Wearable tech acts as alerts, notifying users of important health metrics and encouraging proactive health management.
Addressing Privacy and Health Concerns in Wearable Tech
Wearable technology raises concerns for privacy and health due to the colossal amount of personal data collected. To address these, strong data protection measures are essential, ensuring that sensitive health information is securely stored and shared only with consent. Providing users with control over their data is one of the ways to build user trust. It includes enabling them to opt in, access, or delete the data in question. Regulators should establish clear guidelines, ensuring wearables ensure the compliances with data protection regulations like HIPPA, GDPR or DPDP Act, whichever is applicable as per the jurisdiction. Furthermore, global standards for data encryption, device security, and user privacy should be implemented to mitigate risks. Transparency in data usage and consistent updates to software security are also crucial for protecting users' privacy and health while promoting the responsible use of wearable tech.
CyberPeace Insights
- Making informed decisions about wearable tech starts with thorough research. Start by reading reviews and comparing products to assess their features, compatibility, and security standards.
- Investigate the manufacturer’s reputation for data protection and device longevity. Understanding device capabilities is crucial. One should evaluate whether the wearable meets their needs, such as fitness tracking, health monitoring, or communication features. Consider software security and updates, and data accuracy when comparing options. Opt for devices that offer two-factor authentication for an additional layer of security.
- Check the permissions requested by the accompanying app; only grant access to data that is necessary for the device's functionality. Always read the terms of use to understand your rights and responsibilities regarding the use of the device. Review and customize data-sharing settings for better control to prevent unauthorised access.
- Staying updated on the tech is equally important. A user should follow the advancements in wearable technology be it regular security updates, or regulatory changes that may affect privacy and usability. This ensures getting tech that aligns with user lifestyle while meeting privacy and security expectations.
Conclusion
Privacy and Misinformation are key concerns that emerge due to the use of wearable tech designed to offer benefits such as health monitoring, fitness tracking, and personal convenience. It requires a combination of informed decision-making by users and stringent regulatory oversight to overcome the issues that emerge due to misinformation about these devices. Users must ensure they understand the capabilities and limitations of their devices, from data accuracy to privacy risks. Additionally, manufacturers and regulators need to prioritise transparency, data protection, and compliance with global standards like GDPR or DPDP to build trust. As wearable tech continues to evolve, a balanced approach to innovation and privacy will be essential in fostering its responsible and beneficial use for all.
References
- https://thehealthcaretechnologyreport.com/privacy-data-security-concerns-rise-as-healthcare-wearables-gain-popularity/
- https://journals.plos.org/digitalhealth/article?id=10.1371/journal.pdig.0000104
- https://www.marketsandmarkets.com/Market-Reports/wearable-electronics-market-983.html?gclid=Cj0KCQjwgMqSBhDCARIsAIIVN1V0sqrk6SpYSga3rcDtWcwh8npZ08L0_s4X91gh7yPAa6QmsctB-lMaAlpqEALw_wcB
- https://www.cambridge.org/core/journals/legal-information-management/article/health-data-on-the-go-navigating-privacy-concerns-with-wearable-technologies/05DAF11EFA807051362BB39260C4814C

Executive Summary:
The viral video circulating on social media about the Indian men’s 4x400m relay team recently broke the Asian record and qualified for the finals of the world Athletics championship. The fact check reveals that this is not a recent event but it is from the World World Athletics Championships, August 2023 that happened in Budapest, Hungary. The Indian team comprising Muhammed Anas Yahiya, Amoj Jacob, Muhammed Ajmal Variyathodi, and Rajesh Ramesh, clocked a time of 2 minutes 59.05 seconds, finishing second behind the USA and breaking the Asian record. Although they performed very well in the heats, they only got fifth place in the finals. The video is being reuploaded with false claims stating its a recent record.

Claims:
A recent claim that the Indian men’s 4x400m relay team set the Asian record and qualified to the world finals.




Fact Check:
In the recent past, a video of the Indian Men’s 4x400m relay team which set a new Asian record is viral on different Social Media. Many believe that this is a video of the recent achievement of the Indian team. Upon receiving the posts, we did keyword searches based on the input and we found related posts from various social media. We found an article published by ‘The Hindu’ on August 27, 2023.

According to the article, the Indian team competed in the World Athletics Championship held in Budapest, Hungary. During that time, the team had a very good performance. The Indian team, which consisted of Muhammed Anas Yahiya, Amoj Jacob, Muhammed Ajmal Variyathodi, and Rajesh Ramesh, completed the race in 2:58.47 seconds, coming second after the USA in the event.
The earlier record was 3.00.25 which was set in 2021.

This was a new record in Asia, so it was a historic moment for India. Despite their great success, this video is being reshared with captions that implies this is a recent event, which has raised confusion. We also found various social media posts posted on Aug 26, 2023. We also found the same video posted on the official X account of Prime Minister Narendra Modi, the caption of the post reads, “Incredible teamwork at the World Athletics Championships!
Anas, Amoj, Rajesh Ramesh, and Muhammed Ajmal sprinted into the finals, setting a new Asian Record in the M 4X400m Relay.
This will be remembered as a triumphant comeback, truly historical for Indian athletics.”

This reveals that this is not a recent event but it is from the World World Athletics Championships, August 2023 that happened in Budapest, Hungary.
Conclusion:
The viral video of the recent news about the Indian men’s 4x400m relay team breaking the Asian record is not true. The video was from August 2023 that happened at the World Athletics Championships, Budapest. The Indian team broke the Asian record with 2 minutes 59.05 seconds in second position while the US team obtained first position with a timing of 2 minutes 58.47 seconds. However, the video circulated projecting as a recent event is misleading and false.
- Claim: Recent achievement of the Indian men's 4x400m relay team broke the Asian record and qualified for the World finals.
- Claimed on: X, LinkedIn, Instagram
- Fact Check: Fake & Misleading

A Foray into the Digital Labyrinth
In our digital age, the silhouette of truth is often obfuscated by a fog of technological prowess and cunning deception. With each passing moment, the digital expanse sprawls wider, and within it, synthetic media, known most infamously as 'deepfakes', emerge like phantoms from the machine. These adept forgeries, melding authenticity with fabrication, represent a new frontier in the malleable narrative of understood reality. Grappling with the specter of such virtual deceit, social media behemoths Facebook and YouTube have embarked on a prodigious quest. Their mission? To formulate robust bulwarks around the sanctity of fact and fiction, all the while fostering seamless communication across channels that billions consider an inextricable part of their daily lives.
In an exploration of this digital fortress besieged by illusion, we unpeel the layers of strategy that Facebook and YouTube have unfurled in their bid to stymie the proliferation of these insidious technical marvels. Though each platform approaches the issue through markedly different prisms, a shared undercurrent of necessity and urgency harmonizes their efforts.
The Detailing of Facebook's Strategic
Facebook's encampment against these modern-day chimaeras teems with algorithmic sentinels and human overseers alike—a union of steel and soul. The company’s layer upon layer of sophisticated artificial intelligence is designed to scrupulously survey, identify, and flag potential deepfake content with a precision that borders on the prophetic. Employing advanced AI systems, Facebook endeavours to preempt the chaos sown by manipulated media by detecting even the slightest signs of digital tampering.
However, in an expression of profound acumen, Facebook also serves reminder of AI's fallibility by entwining human discernment into its fabric. Each flagged video wages its battle for existence within the realm of these custodians of reality—individuals entrusted with the hefty responsibility of parsing truth from technologically enabled fiction.
Facebook does not rest on the laurels of established defense mechanisms. The platform is in a perpetual state of flux, with policies and AI models adapting to the serpentine nature of the digital threat landscape. By fostering its cyclical metamorphosis, Facebook not only sharpens its detection tools but also weaves a more resilient protective web, one capable of absorbing the shockwaves of an evolving battlefield.
YouTube’s Overture of Transparency and the Exposition of AI
Turning to the amphitheatre of YouTube, the stage is set for an overt commitment to candour. Against the stark backdrop of deepfake dilemmas, YouTube demands the unveiling of the strings that guide the puppets, insisting on full disclosure whenever AI's invisible hands sculpt the content that engages its diverse viewership.
YouTube's doctrine is straightforward: creators must lift the curtains and reveal any artificial manipulation's role behind the scenes. With clarity as its vanguard, this requirement is not just procedural but an ethical invocation to showcase veracity—a beacon to guide viewers through the murky waters of potential deceit.
The iron fist within the velvet glove of YouTube's policy manifests through a graded punitive protocol. Should a creator falter in disclosing the machine's influence, repercussions follow, ensuring that the ecosystem remains vigilant against hidden manipulation.
But YouTube's policy is one that distinguishes between malevolence and benign use. Artistic endeavours, satirical commentary, and other legitimate expositions are spared the policy's wrath, provided they adhere to the overarching principle of transparency.
The Symbiosis of Technology and Policy in a Morphing Domain
YouTube's commitment to refining its coordination between human insight and computerized examination is unwavering. As AI's role in both the generation and moderation of content deepens, YouTube—which, like a skilled cartographer, must redraw its policies increasingly—traverses this ever-mutating landscape with a proactive stance.
In a Comparative Light: Tracing the Convergence of Giants
Although Facebook and YouTube choreograph their steps to different rhythms, together they compose an intricate dance aimed at nurturing trust and authenticity. Facebook leans into the proactive might of their AI algorithms, reinforced by updates and human interjection, while YouTube wields the virtue of transparency as its sword, cutting through masquerades and empowering its users to partake in storylines that are continually rewritten.
Together on the Stage of Our Digital Epoch
The sum of Facebook and YouTube's policies is integral to the pastiche of our digital experience, a multifarious quilt shielding the sanctum of factuality from the interloping specters of deception. As humanity treads the line between the veracious and the fantastic, these platforms stand as vigilant sentinels, guiding us in our pursuit of an old-age treasure within our novel digital bazaar—the treasure of truth. In this labyrinthine quest, it is not merely about unmasking deceivers but nurturing a wisdom that appreciates the shimmering possibilities—and inherent risks—of our evolving connection with the machine.
Conclusion
The struggle against deepfakes is a complex, many-headed challenge that will necessitate a united front spanning technologists, lawmakers, and the public. In this digital epoch, where the veneer of authenticity is perilously thin, the valiant endeavours of these tech goliaths serve as a lighthouse in a storm-tossed sea. These efforts echo the importance of evergreen vigilance in discerning truth from artfully crafted deception.
References
- https://about.fb.com/news/2020/01/enforcing-against-manipulated-media/
- https://indianexpress.com/article/technology/artificial-intelligence/google-sheds-light-on-how-its-fighting-deep-fakes-and-ai-generated-misinformation-in-india-9047211/
- https://techcrunch.com/2023/11/14/youtube-adapts-its-policies-for-the-coming-surge-of-ai-videos/
- https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/youtube-twitter-hunt-down-deepfakes


