#FactCheck- Pakistan Video Falsely Shared as Attack on Army in West Bengal
Executive Summary:
Assembly elections are underway in several Indian states, including West Bengal, Assam, Kerala, Tamil Nadu, and Puducherry. While voting has already taken place in Assam, Kerala, and Puducherry, polling is still pending in West Bengal. In view of the elections, central security forces have been deployed across West Bengal. Amid this, a video showing a group of people pelting stones at a security vehicle is being widely shared on social media. Some users claim that the incident took place in West Bengal and allege that Muslims attacked an army vehicle. However, research by CyberPeace found the claim to be false. The viral video is from Pakistan and has no connection to West Bengal.
Claim
A social media user shared the video on April 5, 2026, claiming that an army vehicle was attacked in West Bengal.
Post links:

Fact Check
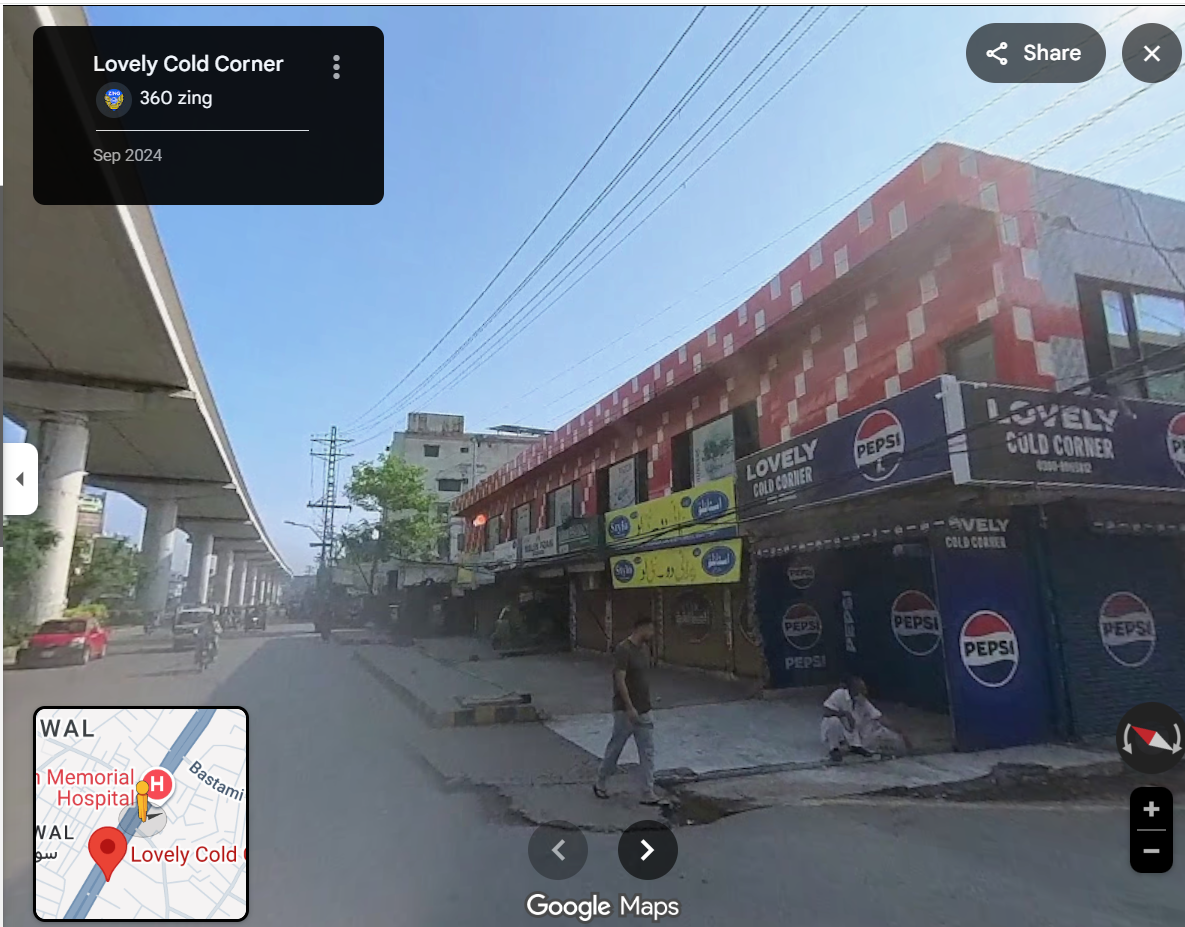
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search using Google Lens. This led us to a video posted on a Facebook page on October 13, 2025. The caption of that post indicated that the video was from Lahore, showing clashes between members of Tehreek-e-Labbaik and the police.

Further clues in the video also pointed to Pakistan. A shop sign reading “Lovely Drink Corner” is visible in the footage. A Google search confirmed that this establishment is located in Lahore, Pakistan.
Conclusion
The viral claim is misleading. Although central forces have been deployed in West Bengal for the ongoing elections, the video showing stone-pelting on a security vehicle is not from the state. It is an old video from Lahore, Pakistan, and is being falsely shared with a communal angle to mislead users.
Related Blogs

Executive Summary
A video is being widely shared on social media amid claims that the BJP has formed a government in West Bengal. The video shows several people being taken away in a bus while their family members are seen crying and grieving nearby. Users sharing the clip claim that the scene is from West Bengal, where the BJP government has allegedly started sending back Bangladeshis who were living illegally in the state.
Research by CyberPeace Research Wing found the viral claim to be misleading. The research revealed that the viral video has no connection with West Bengal. The video is actually from Assam’s Barpeta district, where in 2024, a Foreigners Tribunal declared 28 people as non-citizens. Following the order, authorities shifted them to a transit camp. The viral clip is from that incident. An old and unrelated video is now being falsely shared as a recent incident from West Bengal.
Claim
On May 14, 2026, a Facebook user shared the viral video and wrote, “How sad… Opposition voters are now being packed off to the Bangladesh border from Bengal and Assam. How will they ever win now? Really terrible what is happening to these poor people.” The post link, archive link, and screenshot are provided below.
- https://www.facebook.com/rajendra.kasliwal1/posts/973081982000168/
- https://archive.ph/y7Y4D

Another user also shared the same viral video on social media with a similar claim. The post link, archive link, and screenshot are given below.

Fact Check
To verify the authenticity of the viral video, we extracted several key frames and performed a reverse image search. During the research, we found the same video uploaded on a YouTube channel named Daily Salar Digital on September 5, 2024. The link to the post and its screenshot are given below.

Further research led us to a report published by IndiaTodayNE on September 3, 2024, carrying a similar description of the incident. The post link and screenshot are provided below.

Conclusion
Our research found that the viral video has no connection with West Bengal. The clip is from Assam’s Barpeta district, where in 2024, 28 people were declared non-citizens by a Foreigners Tribunal and later shifted to a transit camp by authorities. The video being shared online is from that incident. An old and unrelated video is being falsely circulated as a recent development from West Bengal.

Introduction
In recent years, the city of Hyderabad/Cyberabad has emerged as a technology hub, a place with the strong presence of multi corporations, Startups, and research institutions, Hyderabad has become a hub of innovations and technological advancement. However, this growing land of cyber opportunities has also become a hub for cybercriminals as well. In this blog post, we shall explore the reasons why professionals are being targeted and the effects of cyber fraud on techies. Through this investigation, we hope to raise awareness about the seriousness of the problem as well as give vital insights and techniques for Cyberabad’s computer workers to defend themselves against cyber theft. We can work together to make Cyberabad’s technology ecosystem safer and more secure.
Defining Cyber Fraud
In today’s age, where everything has an interconnected digital world, cyber fraud cases are increasing daily. Cyber fraud encompasses a wide range of threats and techniques employed by bad actors, such as Phishing, Ransomware, identity theft, online scams, data breaches, and fake websites designed for users. The sophistication of cyber fraud techniques is constantly evolving, making it challenging for individuals and organisations to stay ahead. Cybercriminals use software vulnerabilities, social engineering tactics, and flaws in cybersecurity defences to carry out their harmful operations. Individuals and organisations must grasp these dangers and tactics to protect themselves against cyber fraud.
Impact of Cyber Frauds
The consequences of Falling victim to cyber fraud can be devastating, both personally and professionally. The emotional and financial toll on individuals may be a challenge. Identity theft may lead to damaged credit scores, fraudulent transactions, and years of recovery work to rehabilitate one’s image. Financial fraud can result in depleted bank accounts, unauthorised charges, and substantial monetary losses. Furthermore, being tricked and violated in the digital environment can generate anxiety, tension, and a lack of confidence.
The impact of cyber fraud goes beyond immediate financial losses and can have long-term consequences for individuals’ and organisations’ entire well-being and stability. As the threat environment evolves, it is critical for people and organisations to recognise the gravity of these repercussions and take proactive actions to protect themselves against cyber theft.

Why are Cyberabad Tech Professionals Targeted?
Tech professionals in Cyberabad are particularly vulnerable to cyber due to various factors. Firstly, their expertise and knowledge in technology make them attractive targets for cybercrooks. These professionals possess valuable coding, Software, and administration skills, making them attractive to cybercriminals.
Secondly, the nature of work often involves enormous use of technology, including regular internet contacts, email exchanges, and access to private information. This expanded digital presence exposes them to possible cyber dangers and makes them more vulnerable to fraudsters’ social engineering efforts. Furthermore, the fast-moving nature of the tech industry, with many deadlines and work pressure to deliver, can create a distraction. This can let them click on some malicious links or share sensitive information unknowingly all these factors let the cyber criminals exploit vulnerabilities.
Unveiling the Statistics
According to various reports, 80% of cyber fraud victims in Hyderabad are techies; the rest are the public targeted by cyber crooks. This surprising number emphasises the critical need to address the vulnerabilities and threats this specific segment within the IT community faces.
Going further into the data, we can acquire insights into the many forms of cyber fraud targeting tech workers, the strategies used by cybercriminals, and the impact these occurrences have on individuals and organisations. Examining precise features and patterns within data might give important information for developing successful preventative and protection methods.
Factors Contributing
Several reasons contribute to the elevated risk of cyber fraud among ICT professionals in Cyberabad. Understanding these aspects helps explain why this group is specifically targeted and may be more vulnerable to such assaults.
Technical Expertise: Tech workers frequently have specialised technical knowledge, but this knowledge may only sometimes extend to cybersecurity. Their primary concentration is writing software, designing systems, or implementing technologies, which may result in missing possible vulnerabilities or a lack of overall cybersecurity understanding.
Confidence in Technology: IT workers have a higher level of confidence in technology because of their knowledge and dependence on technology. This trust can sometimes make individuals more vulnerable to sophisticated frauds or social engineering approaches that prey on their faith in the services they utilise.
Time Constraints and Pressure: Tech workers frequently operate under tight deadlines and tremendous pressure to reach project milestones. This may result in hurried decision-making or disregarding possible warning signals of cyber fraud, rendering them more exposed to assaults that prey on time-sensitive circumstances.
Cybercriminals know that technology workers have valuable knowledge, trade secrets, and intellectual property that may be economically profitable. As a result, they are attractive targets for attacks aiming at stealing sensitive data or gaining unauthorised access to critical systems.
The best practices that cyber techies can apply to safeguard their personal and professional data by following these simple tips:
Strong Passwords: create a strong password, using passwords for all your online accounts and changing them regularly. Remember to use unique combinations!
MFA (Multi-Factor Authentication): Enable MFA wherever possible. This provides an extra degree of protection by requiring a second form of verification, such as a code texted to your mobile device and your password.
Use Secured WiFi: Use secure and encrypted Wi-Fi networks, especially while viewing sensitive information. Avoid connecting to public or unprotected networks, as they can be readily exploited. Recognising Red Flags and Staying Ahead
Social Engineering: Be sceptical of unwanted solicitations or offers, both online and offline. Cybercriminals may try to persuade or fool you using social engineering tactics. Before revealing any personal or private information, think critically and confirm the veracity of the request.
Secure Web Browsing: Only browse trustworthy websites with valid SSL certificates (look for “https://” in the URL). Avoid clicking on strange links or downloading files from unknown sources since they may contain malware or ransomware.
Report Suspicious actions: If you encounter any suspicious or fraudulent actions, report them to the relevant authorities, such as the Cyber Crime Police or your organisation’s IT department. Reporting events can assist in avoiding additional harm and aid in identifying and apprehending hackers.
Stay Current on Security Practises: Stay up to speed on the newest cybersecurity risks and best practices. Follow credible sources, participate in cybersecurity forums or seminars, and remain current on new threats and preventative measures.

Conclusion
The rise in cybercrimes and fraud cases among tech experts in Cyberabad is a disturbing trend that requires prompt intervention. We can establish a safer tech cluster that lives on creativity, trust, and resilience by adopting proactive actions, raising awareness, and encouraging cooperation. Let us work together to prevent cybercrime and ensure the future of Cyberabad’s IT ecosystem.

Introduction
The Telecom Regulatory Authority of India (TRAI), on March 13 2023, published a new rule to regulate telemarketing firms. Trai has demonstrated strictness when it comes to bombarding users with intrusive marketing pitches. In a report, TRAI stated that 10-digit mobile numbers could not be utilised for advertising. In reality, different phone numbers are given out for regular calls and telemarketing calls. Hence, it is an appropriate and much-required move in order to suppress and eradicate phishing scammers and secure the Indian Cyber-ecosystem at large.
What are the new rules?
The rules state that now 10-digit unregistered mobile numbers for promotional purposes would be shut down over the following five days. The rule claim that calling from unregistered mobile numbers had been banned was published on February 16. In this case, using 10-digit promotional messages for promotional calling will end within the following five days. This step by TRAI has been seen after nearly 6-8 months of releasing the Telecommunication Bill, 2022, which has focused towards creating a stable Indian Telecom market and reducing the phoney calls/messages by bad actors to reduce cyber crimes like phishing. This is done to distinguish between legitimate and promotional calls. According to certain reports, some telecom firms allegedly break the law by using 10-digit mobile numbers to make unwanted calls and send promotional messages. All telecom service providers must execute the requirements under the recent TRAI directive within five days.
How will the new rules help?
The promotional use of a cellphone number with 10 digits was allowed since the start, however, with the latest NCRB report on cyber crimes and the rising instances and reporting of cyber crimes primarily focused towards frauds related to monetary gains by the bad actors points to the issue of unregulated promotional messages. This move will act as a critical step towards eradicating scammers from the cyber-ecosystem, TRAI has been very critical in understanding the dynamics and shortcomings in the regulation of the telecom spectrum and network in India and has shown keen interest towards suppressing the modes of technology used by the scammers. It is a fact that the invention of the technology does not define its use, the policy of the technology does, hence it is important to draft ad enact policies which better regulate the existing and emerging technologies.
What to avoid?
In pursuance of the rules enacted by TRAI, the business owners involved in promotional services through 10-digit numbers will have to follow these steps-
- It is against the law to utilise a 10-digit cellphone number for promotional calls.
- You should stop doing so right now.
- Your mobile number will be blocked in the following five days if not.
- Users employed by telemarketing firms are encouraged to refrain from using the system in such circumstances.
- Those working for telemarketing firms are encouraged not to call from their mobile numbers.
- Users should phone the company’s registered mobile number for promotional purposes.
Conclusion
The Indian netizen has been exposed to the technology a little later than the western world. However, this changed drastically during the Covid-19 pandemic as the internet and technology penetration rates increased exponentially in just a couple of months. Although this has been used as an advantage by the bad actors, it was pertinent for the government and its institutions to take an effective and efficient step to safeguard the people from financial fraud. Although these frauds occur in high numbers due to a lack of knowledge and awareness, we need to work on preventive solutions rather than precautionary steps and the new rules by TRAI point towards a safe, secured and sustainable future of cyberspace in India.


