#FactCheck - Viral Video of Aircraft Carrier Destroyed in Sea Storm Is AI-Generated
Social media users are widely sharing a video claiming to show an aircraft carrier being destroyed after getting trapped in a massive sea storm. In the viral clip, the aircraft carrier can be seen breaking apart amid violent waves, with users describing the visuals as a “wrath of nature.”
However, CyberPeace Foundation’s research has found this claim to be false. Our fact-check confirms that the viral video does not depict a real incident and has instead been created using Artificial Intelligence (AI).
Claim:
An X (formerly Twitter) user shared the viral video with the caption,“Nature’s wrath captured on camera.”The video shows an aircraft carrier appearing to be devastated by a powerful ocean storm. The post can be viewed here, and its archived version is available here.
https://x.com/Maailah1712/status/2011672435255624090

Fact Check:
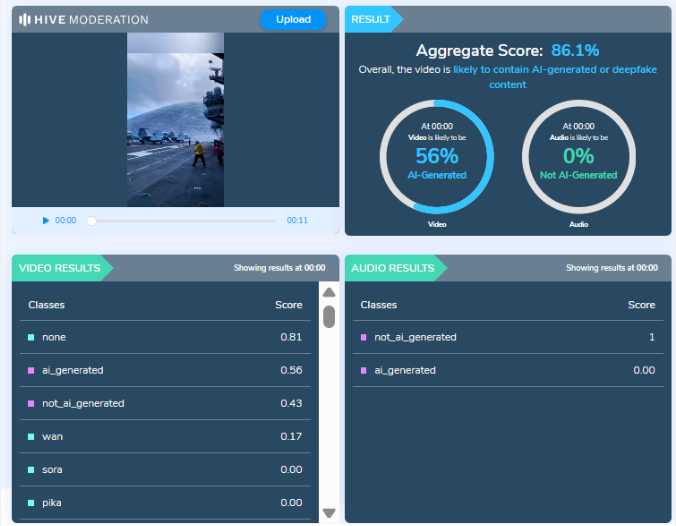
At first glance, the visuals shown in the viral video appear highly unrealistic and cinematic, raising suspicion about their authenticity. The exaggerated motion of waves, structural damage to the vessel, and overall animation-like quality suggest that the video may have been digitally generated. To verify this, we analyzed the video using AI detection tools.
The analysis conducted by Hive Moderation, a widely used AI content detection platform, indicates that the video is highly likely to be AI-generated. According to Hive’s assessment, there is nearly a 90 percent probability that the visual content in the video was created using AI.
Conclusion
The viral video claiming to show an aircraft carrier being destroyed in a sea storm is not related to any real incident.It is a computer-generated, AI-created video that is being falsely shared online as a real natural disaster. By circulating such fabricated visuals without verification, social media users are contributing to the spread of misinformation.
Related Blogs
.webp)
Introduction
In an era where organisations are increasingly interdependent through global supply chains, outsourcing and digital ecosystems, third-party risk has become one of the most vital aspects of enterprise risk management. The SolarWinds hack, the MOVEit vulnerabilities and recent software vendor attacks all serve as a reminder of the necessity to enhance Third-Party Risk Management (TPRM). As cyber risks evolve and become more sophisticated and as regulatory oversight sharpens globally, 2025 is a transformative year for the development of TPRM practices. This blog explores the top trends redefining TPRM in 2025, encompassing real-time risk scoring, AI-driven due diligence, harmonisation of regulations, integration of ESG, and a shift towards continuous monitoring. All of these trends signal a larger movement towards resilience, openness and anticipatory defence in an increasingly dependent world.
Real-Time and Continuous Monitoring becomes the Norm
The old TPRM methods entailed point-in-time testing, which typically was an annual or onboarding process. By 2025, organisations are shifting towards continuous, real-time monitoring of their third-party ecosystems. Now, authentic advanced tools are making it possible for companies to take a real-time pulse of the security of their vendors by monitoring threat indicators, patching practices and digital footprint variations. This change has been further spurred by the growth in cyber supply chain attacks, where the attackers target vendors to gain access to bigger organisations. Real-time monitoring software enables the timely detection of malicious activity, equipping organisations with a faster defence response. It also guarantees dynamic risk rating instead of relying on outdated questionnaire-based scoring.
AI and Automation in Risk Assessment and Due Diligence
Manual TPRM processes aren't sustainable anymore. In 2025, AI and machine learning are reshaping the TPRM lifecycle from onboarding and risk classification to contract review and incident handling. AI technology can now analyse massive amounts of vendor documentation and automatically raise red flags on potential issues. Natural language processing (NLP) is becoming more common for automated contract intelligence, which assists in the detection of risky clauses or liability gaps or data protection obligations. In addition, automation is increasing scalability for large organisations that have hundreds or thousands of third-party relationships, eliminating human errors and compliance fatigue. However, all of this must be implemented with a strong focus on security, transparency, and ethical AI use to ensure that sensitive vendor and organisational data remains protected throughout the process.
Risk Quantification and Business Impact Mapping
Risk scoring in isolation is no longer adequate. One of the major trends for 2025 is the merging of third-party risk with business impact analysis (BIA). Organisations are using tools that associate vendors to particular business processes and assets, allowing better knowledge of how a compromise of a vendor would impact operations, customer information or financial position. This movement has resulted in increased use of risk quantification models, such as FAIR (Factor Analysis of Information Risk), which puts dollar values on risks associated with vendors. By using the language of business value, CISOs and risk officers are more effective at prioritising risks and making resource allocations.
Environmental, Social, and Governance (ESG) enters into TPRM
As ESG keeps growing on the corporate agenda, organisations are taking TPRM one step further than cybersecurity and legal risks and expanding it to incorporate ESG-related factors. In 2025, organisations evaluate if their suppliers have ethical labour practices, sustainable supply chains, DEI (Diversity, Equity, Inclusion) metrics and climate impact disclosures. This growth is not only a reputational concern, but also a third-party non-compliance with ESG can now invoke regulatory or shareholder action. ESG risk scoring software and vendor ESG audits are becoming components of onboarding and performance evaluations.
Shared Assessments and Third-Party Exchanges
With the duplication of effort by having multiple vendors respond to the same security questionnaires, the trend is moving toward shared assessments. Systems such as the SIG Questionnaire (Standardised Information Gathering) and the Global Vendor Exchange allow vendors to upload once and share with many clients. This change not only simplifies the due diligence process but also enhances data accuracy, standardisation and vendor experience. In 2025, organisations are relying more and more on industry-wide vendor assurance platforms to minimise duplication, decrease costs and maximise trust.
Incident Response and Resilience Partnerships
Another trend on the rise is bringing vendors into incident response planning. In 2025, proactive organisations address major vendors as more than suppliers but as resilience partners. This encompasses shared tabletop exercises, communication procedures and breach notification SLAs. With the increasing ransomware attacks and cloud reliance, organisations are now calling for vendor-side recovery plans, RTO and RPO metrics. TPRM is transforming into a comprehensive resilience management function where readiness and not mere compliance takes centre stage.
Conclusion
Third-Party Risk Management in 2025 is no longer about checklists and compliance audits; it's a dynamic, intelligence-driven and continuous process. With regulatory alignment, AI automation, real-time monitoring, ESG integration and resilience partnerships leading the way, organisations are transforming their TPRM programs to address contemporary threat landscapes. As digital ecosystems grow increasingly complex and interdependent, managing third-party risk is now essential. Early adopters who invest in tools, talent and governance will be more likely to create secure and resilient businesses for the AI era.
References
- https://finance.ec.europa.eu/publications/digital-operational-resilience-act-dora_en
- https://digital-strategy.ec.europa.eu/en/policies/nis2-directive
- https://www.meity.gov.in/data-protection-framework
- https://securityscorecard.com
- https://sharedassessments.org/sig/
- https://www.fairinstitute.org/fair-model

Executive Summary:
A viral video claiming the crash site of Air India Flight AI-171 in Ahmedabad has misled many people online. The video has been confirmed not to be from India or a recent crash, but was filmed at Universal Studios Hollywood on a TV or movie set meant to look like a plane crash set piece for a movie.

Claim:
A video that purportedly shows the wreckage of Air India Flight AI-171 after crashing in Ahmedabad on June 12, 2025, has circulated among social media users. The video shows a large amount of aircraft wreckage as well as destroyed homes and a scene reminiscent of an emergency, making it look genuine.

Fact check:
In our research, we took screenshots from the viral video and used reverse image search, which matched visuals from Universal Studios Hollywood. It became apparent that the video is actually from the most famous “War of the Worlds" set, located in Universal Studios Hollywood. The set features a 747 crash scene that was constructed permanently for Steven Spielberg's movie in 2005. We also found a YouTube video. The set has fake smoke poured on it, with debris scattered about and additional fake faceless structures built to represent a scene with a larger crisis. Multiple videos on YouTube here, here, and here can be found from the past with pictures of the tour at Universal Studios Hollywood, the Boeing 747 crash site, made for a movie.


The Universal Studios Hollywood tour includes a visit to a staged crash site featuring a Boeing 747, which has unfortunately been misused in viral posts to spread false information.

While doing research, we were able to locate imagery indicating that the video that went viral, along with the Universal Studios tour footage, provided an exact match and therefore verified that the video had no connection to the Ahmedabad incident. A side-by-side comparison tells us all we need to know to uncover the truth.


Conclusion:
The viral video claiming to show the aftermath of the Air India crash in Ahmedabad is entirely misleading and false. The video is showing a fictitious movie set from Universal Studios Hollywood, not a real disaster scene in India. Spreading misinformation like this can create unnecessary panic and confusion in sensitive situations. We urge viewers to only trust verified news and double-check claims before sharing any content online.
- Claim: Massive explosion and debris shown in viral video after Air India crash.
- Claimed On: Social Media
- Fact Check: False and Misleading

Introduction
In todays time, we can access any information in seconds and from the comfort of our homes or offices. The internet and its applications have been substantial in creating an ease of access to information, but the biggest question which still remains unanswered is Which information is legit and which one is fake? As netizens, we must be critical of what information we access and how.
Influence of Bad actors
The bad actors are one of the biggest threats to our cyberspace as they make the online world full of fear and activities which directly impact the users financial or emotional status by exploitaing their vulnerabilities and attacking them using social engineering. One such issue is website spoofing. In website spoofing, the bad actors try and create a website similar to the original website of any reputed brand. The similarity is so uncanny that the first time or occasional website users find it very difficult to find the difference between the two websites. This is basically an attempt to access sensitive information, such as personal and financial information, and in some cases, to spread malware into the users system to facilitate other forms of cybercrimes. Such websites will have very lucrative offers or deals, making it easier for people to fall prey to such phoney websites In turn, the bad actors can gain sensitive information right from the users without even calling or messaging them.
The Incident
A Noida based senior citizen couple was aggreved by using their dishwasher, and to get it fixed, they looked for the customer care number on their web browser. The couple came across a customer care number- 1800258821 for IFB, a electronics company. As they dialed the number and got in touch with the fake customer care representative, who, upon hearing the couple’s issue, directed them to a supposedly senior official of the company. The senior official spoke to the lady, despite of the call dropping few times, he was admant on staying in touch with the lady, once he had established the trust factor, he asked the lady to download an app which he potrayed to be an app to register complaints and carry out quick actions. The fake senior offical asked the lady to share her location and also asked her to grant few access permissions to the application along with a four digit OTP which looked harmless. He further asked the kady to make a transaction of Rs 10 as part of the complaint processing fee. Till this moment, the couple was under the impression that their complaimt had been registred and the issue with their dishwasher would be rectified soon.
The couple later at night recieved a message from their bank, informing them that Rs 2.25 lakh had been debited from their joint bank account, the following morning, they saw yet another text message informing them of a debit of Rs 5.99 lakh again from their account. The couple immediatly understood that they had become victims to cyber fraud. The couple immediatly launched a complaint on the cyber fraud helpline 1930 and their respective bank. A FIR has been registerd in the Noida Cyber Cell.
How can senior citizens prevent such frauds?
Senior citizens can be particularly vulnerable to cyber frauds due to their lack of familiarity with technology and potential cognitive decline. Here are some safeguards that can help protect them from cyber frauds:
- Educate seniors on common cyber frauds: It’s important to educate seniors about the most common types of cyber frauds, such as phishing, smishing, vishing, and scams targeting seniors.
- Use strong passwords: Encourage seniors to use strong and unique passwords for their online accounts and to change them regularly.
- Beware of suspicious emails and messages: Teach seniors to be wary of suspicious emails and messages that ask for personal or financial information, even if they appear to be from legitimate sources.
- Verify before clicking: Encourage seniors to verify the legitimacy of links before clicking on them, especially in emails or messages.
- Keep software updated: Ensure seniors keep their software, including antivirus and operating system, up to date.
- Avoid public Wi-Fi: Discourage seniors from using public Wi-Fi for sensitive transactions, such as online banking or shopping.
- Check financial statements: Encourage seniors to regularly check their bank and credit card statements for any suspicious transactions.
- Secure devices: Help seniors secure their devices with antivirus and anti-malware software and ensure that their devices are password protected.
- Use trusted sources: Encourage seniors to use trusted sources when making online purchases or providing personal information online.
- Seek help: Advise seniors to seek help if they suspect they have fallen victim to a cyber fraud. They should contact their bank, credit card company or report the fraud to relevant authorities. Calling 1930 should be the first and primary step.
Conclusion
The cyberspace is new space for people of all generations, the older population is a little more vulnerble in this space as they have not used gadgets or internet for most f theur lives, and now they are dependent upon the devices and application for their convinience, but they still do not understand the technology and its dark side. As netizens, we are responsible for safeguarding the youth and the older population to create a wholesome, safe, secured and sustainable cyberecosystem. Its time to put the youth’s understanding of tech and the life experience of the older poplaution in synergy to create SoPs and best practices for erradicating such cyber frauds from our cyberspace. CyberPeace Foundation has created a CyberPeace Helpline number for victims where they will be given timely assitance for resolving their issues; the victims can reach out the helpline on +91 95700 00066 and thay can also mail their issues on helpline@cyberpeace.net.


