Enhancing Your Privacy on WhatsApp: A Comprehensive Security Guide
Overview:
In today’s digital landscape, safeguarding personal data and communications is more crucial than ever. WhatsApp, as one of the world’s leading messaging platforms, consistently enhances its security features to protect user interactions, offering a seamless and private messaging experience
App Lock: Secure Access with Biometric Authentication
To fortify security at the device level, WhatsApp offers an app lock feature, enabling users to protect their app with biometric authentication such as fingerprint or Face ID. This feature ensures that only authorized users can access the app, adding an additional layer of protection to private conversations.
How to Enable App Lock:
- Open WhatsApp and navigate to Settings.
- Select Privacy.
- Scroll down and tap App Lock.
- Activate Fingerprint Lock or Face ID and follow the on-screen instructions.

Chat Lock: Restrict Access to Private Conversations
WhatsApp allows users to lock specific chats, moving them to a secured folder that requires biometric authentication or a passcode for access. This feature is ideal for safeguarding sensitive conversations from unauthorized viewing.
How to Lock a Chat:
- Open WhatsApp and select the chat to be locked.
- Tap on the three dots (Android) or More Options (iPhone).
- Select Lock Chat
- Enable the lock using Fingerprint or Face ID.

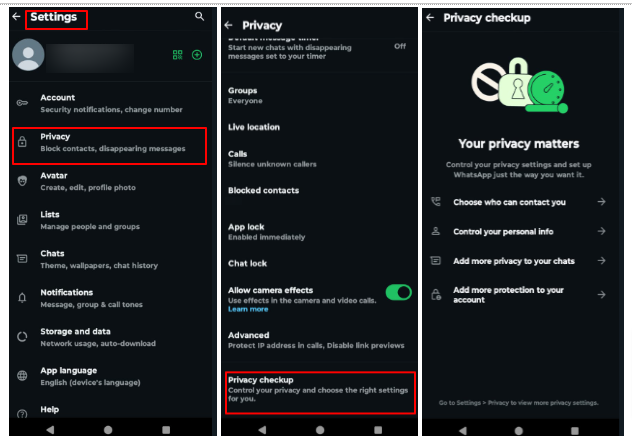
Privacy Checkup: Strengthening Security Preferences
The privacy checkup tool assists users in reviewing and customizing essential security settings. It provides guidance on adjusting visibility preferences, call security, and blocked contacts, ensuring a personalized and secure communication experience.
How to Run Privacy Checkup:
- Open WhatsApp and navigate to Settings.
- Tap Privacy.
- Select Privacy Checkup and follow the prompts to adjust settings.
Automatic Blocking of Unknown Accounts and Messages
To combat spam and potential security threats, WhatsApp automatically restricts unknown accounts that send excessive messages. Users can also manually block or report suspicious contacts to further enhance security.
How to Manage Blocking of Unknown Accounts:
- Open WhatsApp and go to Settings.
- Select Privacy.
- Tap to Advanced
- Enable Block unknown account messages

IP Address Protection in Calls
To prevent tracking and enhance privacy, WhatsApp provides an option to hide IP addresses during calls. When enabled, calls are routed through WhatsApp’s servers, preventing location exposure via direct connections.
How to Enable IP Address Protection in Calls:
- Open WhatsApp and go to Settings.
- Select Privacy, then tap Advanced.
- Enable Protect IP Address in Calls.

Disappearing Messages: Auto-Deleting Conversations
Disappearing messages help maintain confidentiality by automatically deleting sent messages after a predefined period—24 hours, 7 days, or 90 days. This feature is particularly beneficial for reducing digital footprints.
How to Enable Disappearing Messages:
- Open the chat and tap the Chat Name.
- Select Disappearing Messages.
- Choose the preferred duration before messages disappear.

View Once: One-Time Access to Media Files
The ‘View Once’ feature ensures that shared photos and videos can only be viewed a single time before being automatically deleted, reducing the risk of unauthorized storage or redistribution.
How to Send View Once Media:
- Open a chat and tap the attachment icon.
- Choose Camera or Gallery to select media.
- Tap the ‘1’ icon before sending the media file.

Group Privacy Controls: Manage Who Can Add You
WhatsApp provides users with the ability to control group invitations, preventing unwanted additions by unknown individuals. Users can restrict group invitations to ‘Everyone,’ ‘My Contacts,’ or ‘My Contacts Except…’ for enhanced privacy.
How to Adjust Group Privacy Settings:
- Open WhatsApp and go to Settings.
- Select Privacy and tap Groups.
- Choose from the available options: Everyone, My Contacts, or My Contacts Except

Conclusion
WhatsApp continuously enhances its security features to protect user privacy and ensure safe communication. With tools like App Lock, Chat Lock, Privacy Checkup, IP Address Protection, and Disappearing Messages, users can safeguard their data and interactions. Features like View Once and Group Privacy Controls further enhance confidentiality. By enabling these settings, users can maintain a secure and private messaging experience, effectively reducing risks associated with unauthorized access, tracking, and digital footprints. Stay updated and leverage these features for enhanced security.