#FactCheck-Bangladesh Video Falsely Shared as Security Forces Action During West Bengal Elections 2026
Executive Summary
As West Bengal heads for vote counting on May 4, 2026, following the second phase of Assembly polling held on April 29, a video is being widely shared on social media. The clip shows security personnel baton-charging civilians, with users claiming it depicts force being used during the West Bengal Assembly Elections 2026. Research by CyberPeace Research Wing found that the viral claim is misleading. The video is actually from Bangladesh and is being falsely linked to the West Bengal elections to spread confusion.
Claim
A Facebook user named “Adv Mohd Salman” shared the clip on April 29, 2026, using Bengal-related hashtags and claiming that voters standing in line were beaten to influence the election outcome. The post alleged that free and fair voting rights were being suppressed.

Fact Check
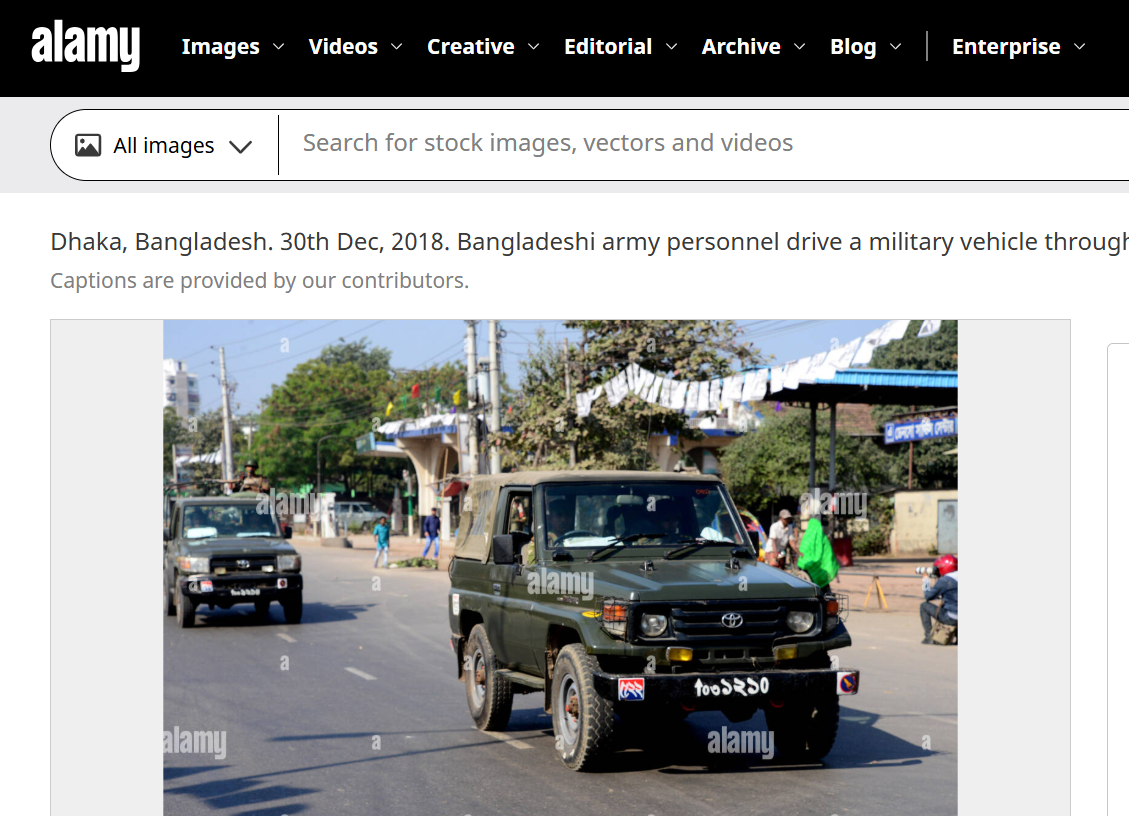
To verify the claim, we closely examined the viral video. A vehicle visible in the footage had a registration number written in a non-Hindi script. Using Google Lens reverse image search, we found a matching image uploaded on Alamy on December 30, 2018. The image showed a military vehicle with the same script and registration style seen in the viral clip.
According to the description on the platform, the image was taken in Dhaka during Bangladesh’s national elections and showed Bangladeshi army personnel moving through a street near a polling station. This confirms that the viral footage is not related to the 2026 West Bengal Assembly elections.
Conclusion
Our research confirms that the video showing security personnel baton-charging civilians is from Bangladesh, not West Bengal. It is being falsely shared as footage from the 2026 West Bengal Assembly elections to mislead users.
Related Blogs

Introduction
In the era of the internet where everything is accessible at your fingertip, a disturbing trend is on the rise- over 90% of websites containing child abuse material now have self-generated images, obtained from victims as young as three years old. A shocking revelation, shared by the (IWF) internet watch foundation, The findings of the IWF have caused concern about the increasing exploitation of children below the age of 10. The alarming trend highlights the increasing exploitation of children under the age of 10, who are coerced, blackmailed, tricked, or groomed into participating in explicit acts online. The IWF's data for 2023 reveals a record-breaking 275,655 websites hosting child sexual abuse material, with 92% of them containing such "self-generated" content.
Disturbing Tactics Shift
Disturbing numbers came that, highlight a distressing truth. In 2023, 275,655 websites were discovered to hold child sexual abuse content, reaching a new record and reflecting an alarming 8% increase over the previous year. What's more concerning is that 92% of these websites had photos or videos generated by the website itself. Surprisingly, 107,615 of these websites had content involving children under the age of ten, with 2,500 explicitly featuring youngsters aged three to six.
Profound worries
Deep concern about the rising incidence of images taken by extortion or coercion from elementary school-aged youngsters. This footage is currently being distributed on very graphic and specialised websites devoted to child sexual assault. The process begins in a child's bedroom with the use of a camera and includes the exchange, dissemination, and gathering of explicit content by devoted and determined persons who engage in sexual exploitation. These criminals are ruthless. The materials are being circulated via mail, instant messaging, chat rooms, and social media platforms, (WhatsApp, Telegram, Skype, etc.)
Live Streaming of such material involves real-time broadcast which again is a major concern as the nature of the internet is borderless the access to such material is international, national, and regional, which even makes it difficult to get the predators and convict them. With the growth, it has become easy for predators to generate “self-generated “images or videos.
Financial Exploitation in the Shadows: The Alarming Rise of Sextortion
Looking at the statistics globally there have been studies that show an extremely shocking pattern known as “sextortion”, in which adolescents are targeted for extortion and forced to pay money under the threat of exposing images to their families or relatives and friends or on social media. The offender's goal is to obtain sexual gratification.
The financial variation of sextortion takes a darker turn, with criminals luring kids into making sexual content and then extorting them for money. They threaten to reveal the incriminating content unless their cash demands, which are frequently made in the form of gift cards, mobile payment services, wire transfers, or cryptocurrencies, are satisfied. In this situation, the predators are primarily driven by money gain, but the psychological impact on their victims is as terrible. A shocking case was highlighted where an 18-year-old was landed in jail for blackmailing a young girl, sending indecent images and videos to threaten her via Snapchat. The offender was pleaded guilty.
The Question on Security?
The introduction of end-to-end encryption in platforms like Facebook Messenger has triggered concerns within law enforcement agencies. While enhancing user privacy, critics argue that it may inadvertently facilitate criminal activities, particularly the exploitation of vulnerable individuals. The alignment with other encrypted services is seen as a potential challenge, making it harder to detect and investigate crimes, thus raising questions about finding a balance between privacy and public safety.
One of the major concerns in the online safety of children is the implementation of encryption by asserting that it enhances the security of individuals, particularly children, by safeguarding them from hackers, scammers, and criminals. They underscored their dedication to enforcing safety protocols, such as prohibiting adults from texting teenagers who do not follow them and employing technology to detect and counteract bad conduct.
These distressing revelations highlight the urgent need for comprehensive action to protect our society's most vulnerable citizens i.e., children, youngsters, and adolescents throughout the era of digital progress. As experts and politicians grapple with these troubling trends, the need for action to safeguard kids online becomes increasingly urgent.
Role of Technology in Combating Online Exploitation
With the rise of technology, there has been a rise in online child abuse, technology also serves as a powerful tool to combat it. The advanced algorithms and use of Artificial intelligence tools can be used to disseminate ‘self-generated’ images. Additional tech companies can collaborate and develop some effective solutions to safeguard every child and individual.
Role of law enforcement agencies
Child abuse knows no borders, and addressing the issues requires legal intervention at all levels. National, regional, and international law enforcement agencies investigate online child sexual exploitation and abuse and cooperate in the investigation of these cybercrimes, Various investigating agencies need to have mutual legal assistance and extradition, bilateral, and multilateral conventions to conduct to identify, investigate, and prosecute perpetrators of online child sexual exploitation and abuse. Apart from this cooperation between private and government agencies is important, sharing the database of perpetrators can help the agencies to get them caught.
How do you safeguard your children?
Looking at the present scenario it has become a crucial part of protecting and safeguarding our children online against online child abuse here are some practical steps that can help in safeguarding your loved one.
- Open communication: Establish open communication with your children, make them feel comfortable, and share your experiences with them, make them understand what good internet surfing is and educate them about the possible risks without generating fear.
- Teach Online Safety: educate your children about the importance of privacy and the risks associated with it. Teach them strong privacy habits like not sharing any personal information with a stranger on any social media platform. Teach them to create some unique passwords and to make them aware not to click on any suspicious links or download files from unknown sources.
- Set boundaries: As a parent set rules and guidelines for internet usage, set time limits, and monitor their online activities without infringing their privacy. Monitor their social media platforms and discuss inappropriate behaviour or online harassment. As a parent take an interest in your children's online activities, websites, and apps inform them, and teach them online safety measures.
Conclusion
The predominance of self-generated' photos in online child abuse content necessitates immediate attention and coordinated action from governments, technology corporations, and society as a whole. As we negotiate the complicated environment of the digital age, we must be watchful, modify our techniques, and collaborate to defend the innocence of the most vulnerable among us. To combat online child exploitation, we must all work together to build a safer, more secure online environment for children all around the world.
References
- https://www.the420.in/over-90-of-websites-containing-child-abuse-feature-self-generated-images-warns-iwf/
- https://news.sky.com/story/self-generated-images-found-on-92-of-websites-containing-child-sexual-abuse-with-victims-as-young-as-three-13049628
- https://www.firstpost.com/world/russia-rejects-us-proposal-to-resume-talks-on-nuclear-arms-control-13630672.html
- https://www.news4hackers.com/iwf-warns-that-more-than-90-of-websites-contain-self-generated-child-abuse-images/

INTRODUCTION:
The Ministry of Defence has recently designated the Additional Directorate General of Strategic Communication in the Indian Army as the nodal officer now authorised to send removal requests and notices to social media intermediaries regarding posts consisting of illegal content with respect to the Army. Earlier, this process was followed through the Ministry of Electronics and Information Technology (MeitY). The recent designation gives the Army the autonomy of circumnavigating the old process and enables them to send direct notices (as deemed appropriate by the government and its agency). Let us look at the legal framework that allows them to do so and its policy implications.
BACKGROUND AND LEGAL FRAMEWORK:
Section 69 of the IT Act 2000 gives the government the power to issue directions for interception, monitoring or decryption of any data/information through any computer resource. This is done so under six reasons related to:
- Upholding the sovereignty or integrity of India
- Security of the state
- Defence of India
- Friendly relations with foreign states
- Public order or for preventing incitement of any cognisable offence
- Investigations of offences related to the aforementioned reasons
Section 79(3)(b) of the Information Technology Act 2000 is another aspect of the law related to the removal of data on notification. It allows for all intermediaries (including internet service providers and social media platforms) to have safety harbours from the liability of the content put out by third parties/users on their platforms. This, however, is only applicable when the intermediary has either received a notification or actual knowledge by the appropriate government or its agency of the data on their platform being used for unlawful acts and complies promptly by removing the data from their platform without tampering with evidence.
PLAUSIBLE REASONS FOR POLICY DECISION:
Cases related to the Indian Army are sensitive for a number of reasons, rooted in the fact that they directly pertain to the nation's security, integrity and sovereignty. The impact of the spread of misinformation and disinformation is almost instantaneous and the stakes are high in any circumstance, but exceptionally so when it comes to the Armed Forces and the nation’s security status. A mechanism to tackle cases of such a security level should allow for quick action from the authorities. Owing to the change in the ability to notify directly rather than through another ministry, the army can now promptly deal with these concerns as and when they arise. One immediate benefit of this change is that the forces can now quickly respond to instances where foreign states and actors with malicious intent put out information that can cause harm to the nation’s interests, image and integrity.
This step helps the forces deal with countering misinformation, ensuring national security and even addressing issues of online propaganda. An example of sensitive content about the army leading to legal intervention is the case of Delhi-based magazine The Caravan. The Defence Ministry, along with the Intelligence Bureau and the Jammu and Kashmir police ordered the Delhi-based publication to remove an article claiming the murder and torture of civilians by the Indian army in Jammu and Kashmir citing the IT (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021. The instruction was challenged by the magazine in the courts.
CONCLUSION:
This move brings with it potential benefits along with risks and the focus should always be on maintaining a balanced approach. Transparency and accountability are imperative and checks on related guidelines so as to prevent misuse while simultaneously protecting national security should be at the centre of the objective of the policy approach. Misinformation in and about the armed forces must be dealt with immediately.
REFERENCES:
- https://www.hindustantimes.com/india-news/army-can-now-directly-issue-notices-to-remove-online-posts-101730313177838.html
- https://www.hindustantimes.com/india-news/inside-79-3-b-the-content-blocking-provision-with-many-legal-grey-areas-101706987924882.html
- https://www.thehindu.com/news/national/govt-orders-magazine-to-take-down-article-on-army-torture-and-murder-in-jammu/article67840790.ece
- https://myind.net/Home/viewArticle/army-gains-authority-to-directly-issue-notice-to-take-down-online-posts

Executive Summary
A video showing uniformed personnel removing street vendors and damaging roadside stalls is being circulated on social media with the false claim that the Nepal government has started expelling Bangladeshis from the country. The viral clip is around 49 seconds long and shows authorities clearing vendors from a public area. Nepali audio can also be heard in the background, which appears to have added to the misleading narrative.
However, an research by the CyberPeace Research Wing found that the claim is false. The video is not from Nepal, but from Bangladesh’s capital Dhaka, where authorities were carrying out an anti-encroachment operation near the National Stadium.
Claim:
The video was shared on X with a caption claiming that a Hindu-led government in Nepal had begun driving Bangladeshis out of the country.
Fact Check:
A close examination of the video revealed several signs contradicting the claim. Text written in Bengali can be seen at multiple places in the footage. The caps worn by uniformed personnel also appear to display “Bangladesh Police.” Investigators also noticed a stadium-like structure in the background. Comparing the visuals with street-view imagery available on Google Maps led to a match near the National Stadium area in Dhaka, Bangladesh.


Further verification found a video uploaded on March 18, 2025, by a Bangladeshi news portal on YouTube containing scenes matching the viral clip. The caption described it as footage from an anti-encroachment drive in the Gulistan area of Dhaka.

A similar version of the video was also found on a Bangladeshi Instagram account uploaded on March 17, where it was again described as police action against illegal encroachments. The video credit was attributed to a person named Zahir Rehan.
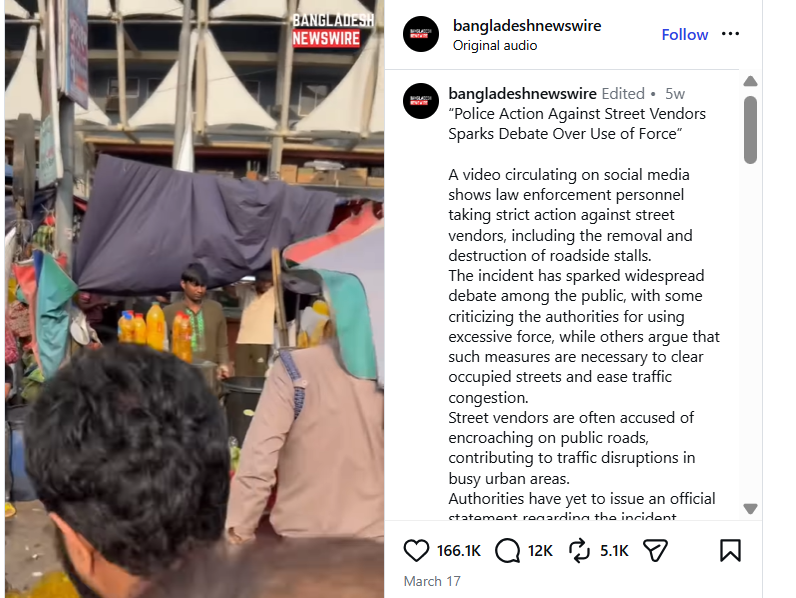
While the exact date of the original footage could not be independently confirmed, available evidence clearly links the video to Bangladesh and not Nepal.
Conclusion:
The viral claim that Nepal has begun expelling Bangladeshis is false. The video actually shows an anti-encroachment drive carried out by authorities in Dhaka, Bangladesh.


