#FactCheck -Scripted Video of Pre-Wedding Roka at Metro Station Misleads Users
Executive Summary
A video is going viral on social media showing a woman performing a pre-wedding ritual called “Roka” for a couple at a metro station. Many users are sharing the clip believing it to be a real incident. CyberPeace found in its research that the viral claim is false. The video is actually scripted.
Claim:
An Instagram user posted the video on February 7, 2026, with the caption, “A mother performed her son’s Roka with his girlfriend at a metro station.”
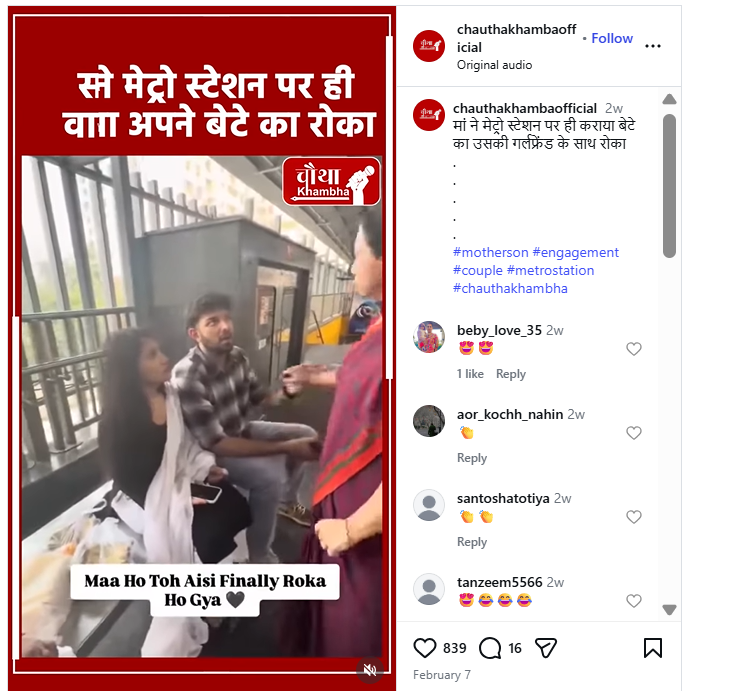
Fact Check:
To verify the claim, we conducted a reverse image search using Google Lens on screenshots from the viral video. We found the same video was first uploaded on February 5, 2026, by an Instagram account named “chalte_phirte098.” The profile belongs to digital content creator Aarav Mavi, who regularly posts relationship and breakup-related videos.
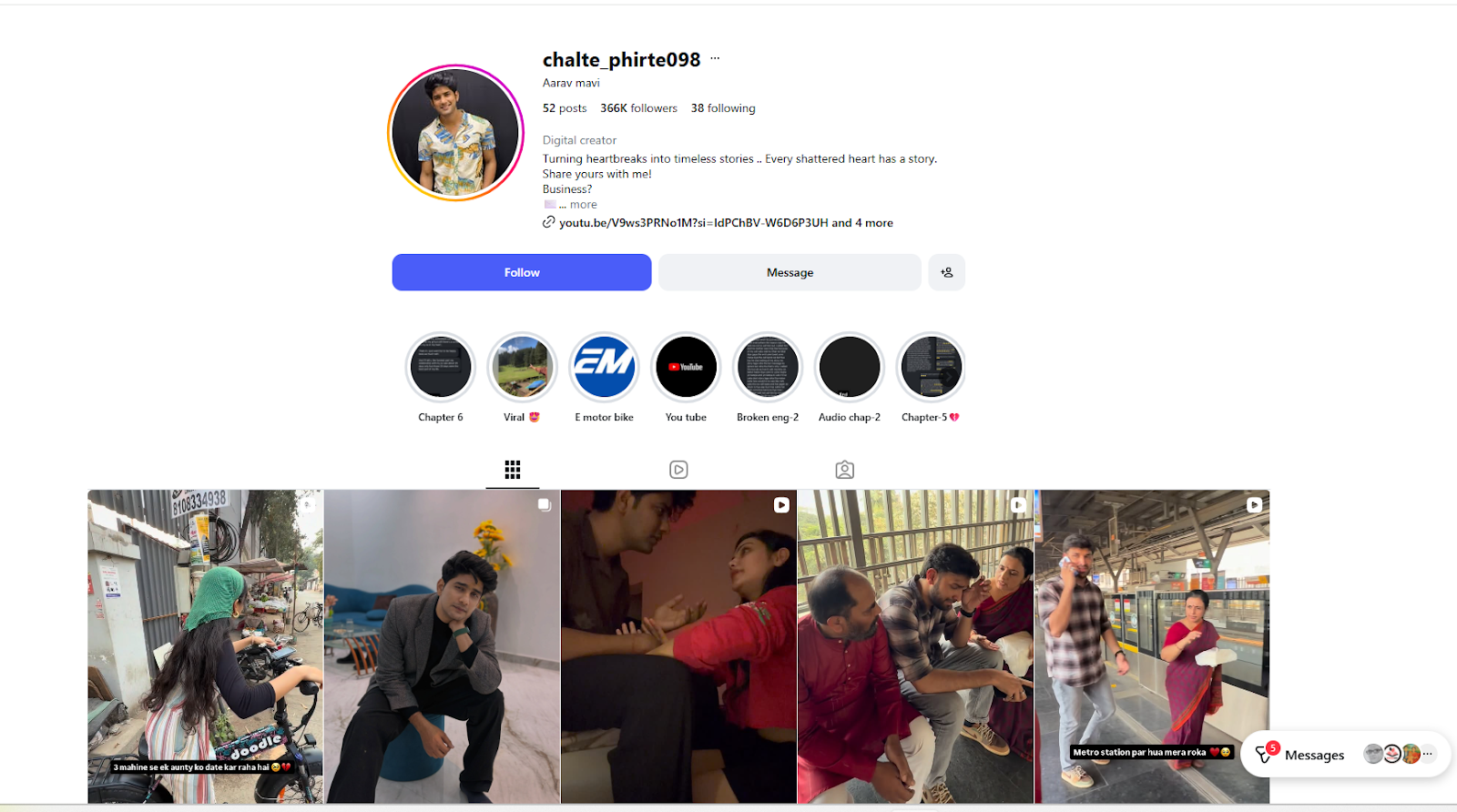
Although the viral clip does not include any disclaimer stating that it is scripted, an older video posted by the creator on December 16, 2025, clarifies that his content is based on real-life stories shared by people but is filmed using professional actors. Several similar staged videos are also available on his profile on Instagram.

Conclusion:
Our research clearly shows that the viral video claiming to show a pre-wedding Roka ceremony at a metro station is not real. It was created by a content creator for entertainment purposes. Therefore, the claim circulating on social media is misleading.
Related Blogs
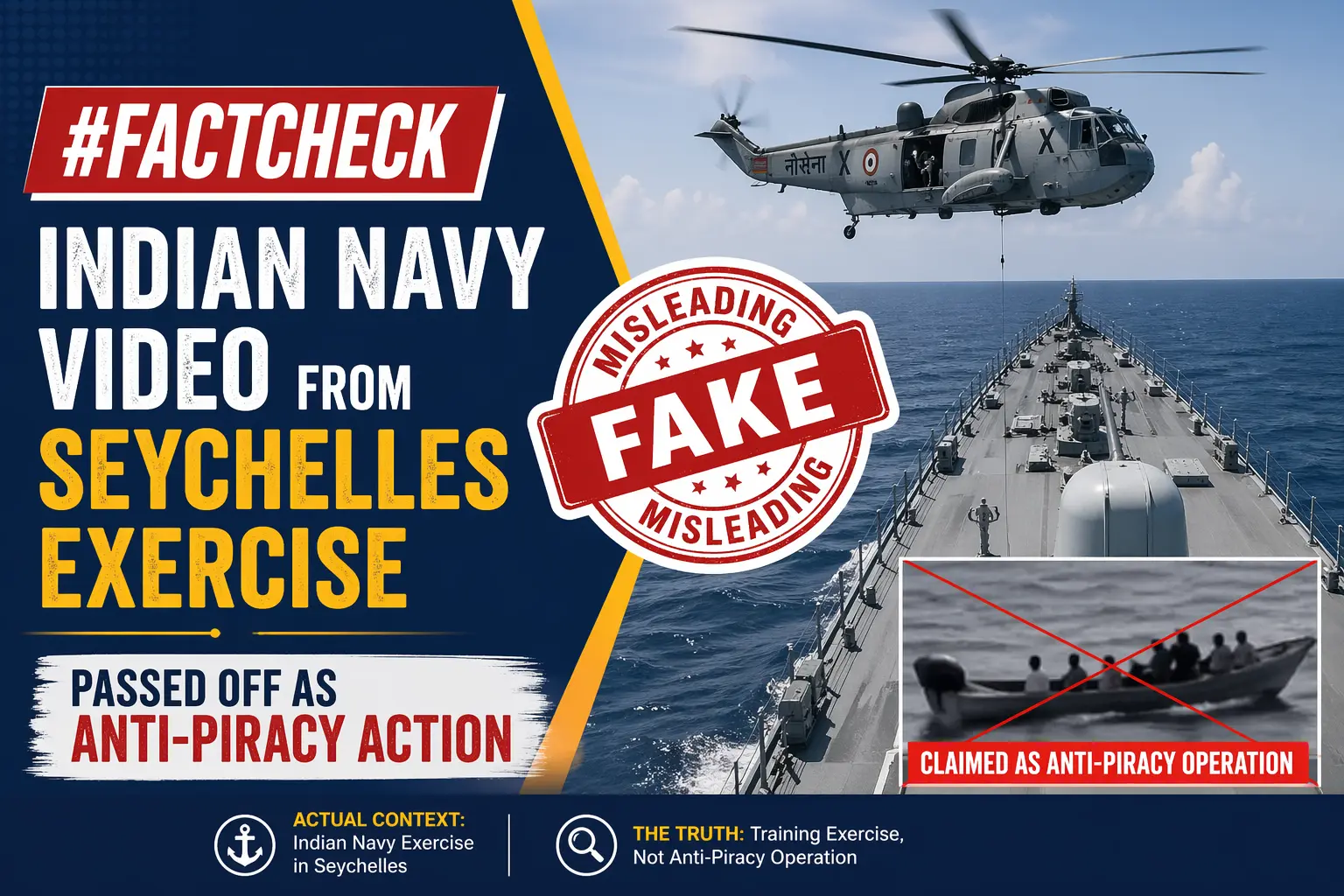
Executive Summary
A video showing armed personnel detaining individuals on board a ship is being widely shared on social media with the claim that Indian Navy’s MARCOS captured 35 Somali pirates during a recent anti-piracy operation. However, research by the CyberPeace Research Wing found the claim to be misleading. The viral video is actually from the joint military exercise ‘LAMITIYE 2026’, held in Seychelles in March, involving the Indian Armed Forces and the Seychelles Defence Forces.
Claim
Users on X (formerly Twitter) shared the clip with captions such as: “Indian Navy MARCOS captured 35 Somali pirates,” presenting it as footage of a recent anti-piracy mission.

Fact Check
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search. This led us to the same video posted on March 20 by a Facebook page named “Defence Squad.” The caption identified the visuals as showing Indian Navy MARCOS and the Seychelles Defence Forces’ Special Operations Unit during the joint military exercise LAMITIYE 2026.
Link:
- https://www.facebook.com/reel/1263962865936234
- https://www.facebook.com/reel/1263962865936234
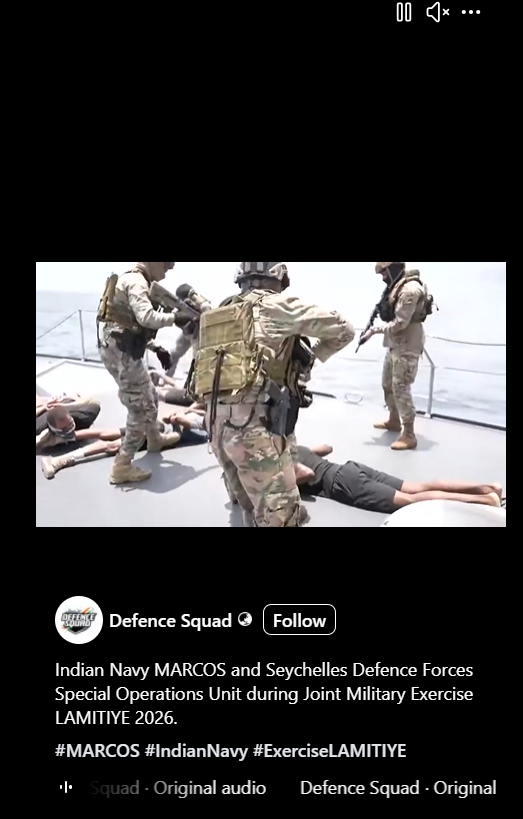
Further keyword searches led to multiple news reports carrying screenshots from the same video. These reports confirmed that the 11th India-Seychelles joint military exercise, LAMITIYE 2026, was conducted in Seychelles from March 9 to March 20.


We did not find any recent reports about the Indian Navy capturing Somali pirates. However, in March 2024, the Indian Navy had captured 35 Somali pirates who had hijacked a bulk carrier and taken hostages. The suspects were later handed over to Mumbai Police for legal proceedings.
Conclusion
The viral claim is misleading. The video being circulated as footage of an anti-piracy operation by the Indian Navy does not show the capture of Somali pirates. Instead, it is from the India-Seychelles joint military exercise ‘LAMITIYE 2026’, conducted in March with the participation of the Indian Armed Forces and the Seychelles Defence Forces. While the Indian Navy had indeed captured 35 Somali pirates in a separate incident in March 2024, there are no credible or recent reports linking such an operation to the viral video. The clip has been taken out of context and is being shared with a false narrative, leading to misinformation about a routine military exercise.

Executive Summary:
The viral social media posts circulating several photos of Indian Army soldiers eating their lunch in the extremely hot weather near the border area in Barmer/ Jaisalmer, Rajasthan, have been detected as AI generated and proven to be false. The images contain various faults such as missing shadows, distorted hand positioning and misrepresentation of the Indian flag and soldiers body features. The various AI generated tools were also used to validate the same. Before sharing any pictures in social media, it is necessary to validate the originality to avoid misinformation.




Claims:
The photographs of Indian Army soldiers having their lunch in extreme high temperatures at the border area near to the district of Barmer/Jaisalmer, Rajasthan have been circulated through social media.




Fact Check:
Upon the study of the given images, it can be observed that the images have a lot of similar anomalies that are usually found in any AI generated image. The abnormalities are lack of accuracy in the body features of the soldiers, the national flag with the wrong combination of colors, the unusual size of spoon, and the absence of Army soldiers’ shadows.




Additionally it is noticed that the flag on Indian soldiers’ shoulder appears wrong and it is not the traditional tricolor pattern. Another anomaly, soldiers with three arms, strengtheness the idea of the AI generated image.
Furthermore, we used the HIVE AI image detection tool and it was found that each photo was generated using an Artificial Intelligence algorithm.


We also checked with another AI Image detection tool named Isitai, it was also found to be AI-generated.


After thorough analysis, it was found that the claim made in each of the viral posts is misleading and fake, the recent viral images of Indian Army soldiers eating food on the border in the extremely hot afternoon of Badmer were generated using the AI Image creation tool.
Conclusion:
In conclusion, the analysis of the viral photographs claiming to show Indian army soldiers having their lunch in scorching heat in Barmer, Rajasthan reveals many anomalies consistent with AI-generated images. The absence of shadows, distorted hand placement, irregular showing of the Indian flag, and the presence of an extra arm on a soldier, all point to the fact that the images are artificially created. Therefore, the claim that this image captures real-life events is debunked, emphasizing the importance of analyzing and fact-checking before sharing in the era of common widespread digital misinformation.
- Claim: The photo shows Indian army soldiers having their lunch in extreme heat near the border area in Barmer/Jaisalmer, Rajasthan.
- Claimed on: X (formerly known as Twitter), Instagram, Facebook
- Fact Check: Fake & Misleading
.webp)
Introduction
The recent events in Mira Road, a bustling suburb on the outskirts of Mumbai, India, unfold like a modern-day parable, cautioning us against the perils of unverified digital content. The Mira Road incident, a communal clash that erupted into the physical realm, has been mirrored and magnified through the prism of social media. The Maharashtra Police, in a concerted effort to quell the spread of discord, issued stern warnings against the dissemination of rumours and fake messages. These digital phantoms, they stressed, have the potential to ignite law and order conflagrations, threatening the delicate tapestry of peace.
The police's clarion call came in the wake of a video, mischievously edited, that falsely claimed anti-social elements had set the Mira Road railway station ablaze. This digital doppelgänger of reality swiftly went viral, its tendrils reaching into the ubiquitous realm of WhatsApp, ensnaring the unsuspecting in its web of deceit.
In this age of information overload, where the line between fact and fabrication blurs, the police urged citizens to exercise discernment. The note they issued was not merely an advisory but a plea for vigilance, a reminder that the act of sharing unauthenticated messages is not a passive one; it is an act that can disturb the peace and unravel the fabric of society.
The Massacre
The police's response to this crisis was multifaceted. Administrators and members of social media groups found to be the harbingers of such falsehoods would face legal repercussions. The Thane District, a mosaic of cultural and religious significance, has been marred by a series of violent incidents, casting a shadow over its storied history. The police, in their role as guardians of order, have detained individuals, scoured social media for inauthentic posts, and maintained a vigilant presence in the region.
The Maharashtra cyber cell, a digital sentinel, has unearthed approximately 15 posts laden with videos and messages designed to sow discord among the masses. These findings were shared with the Mira-Bhayandar, Vasai-Virar (MBVV) police, who stand ready to take appropriate action. Inspector General Yashasvi Yadav of the Maharashtra cyber cell issued an appeal to the public, urging them to refrain from circulating such unverified messages, reinforcing the notion that the propagation of inauthentic information is, in itself, a crime.
The MBVV police, in their zero-tolerance stance, have formed a team dedicated to scrutinizing social media posts. The message is clear: fake news will be met with strict action. The right to free speech on social media comes with the responsibility not to share information that could incite mischief. The Indian Penal Code and Information Technology Act serve as the bulwarks against such transgressions.
The Aftermath
In the aftermath of the clashes, the police have worked tirelessly to restore calm. A young man, whose video replete with harsh and obscene language went viral, was apprehended and has since apologised for his actions. The MBVV police have also taken to social media to reassure the public that the situation is under control, urging them to avoid circulating messages that could exacerbate tensions.
The Thane district has witnessed acts of vandalism targeting shops, further escalating tensions. In response, the police have apprehended individuals linked to these acts, hoping that such measures will expedite the return of peace. Advisories have been issued, warning against the dissemination of provocative messages and rumours.
In total, 19 individuals have been taken into custody in relation to numerous incidents of violence. The Mira-Bhayandar and Vasai-Virar police have underscored their commitment to legal action against those who spread rumours through fake messages. The authorities have also highlighted the importance of brotherhood and unity, reminding citizens that above all, they are Indians first.
Conclusion
In a world where old videos, stripped of context, can fuel tensions, the police have issued a note referring to the aforementioned fake video message. They urge citizens to exercise caution, to neither believe nor circulate such messages. Police Authorities have assured that no one involved in the violence will be spared, and peace committees are being convened to restore harmony. The Mira Road incident serves as a sign of the prowess of information and responsibility that comes with it. In the digital age, where the ephemeral and the eternal collide, we must navigate the waters of truth with care. Ultimately, it is not just the image of a locality that is at stake, but the essence of our collective humanity.
References
- https://youtu.be/gK2Ac1qP-nE?feature=shared
- https://www.mid-day.com/mumbai/mumbai-crime-news/article/mira-road-communal-clash-those-spreading-fake-messages-to-face-strict-action-say-mira-bhayandar-vasai-virar-cops-23331572
- https://www.mid-day.com/mumbai/mumbai-news/article/mira-road-communal-clash-cybercops-on-alert-for-fake-clips-23331653
- https://www.theweek.in/wire-updates/national/2024/01/24/bom43-mh-shops-3rdld-vandalism.html


