#FactCheck - Manipulated Image Alleging Disrespect Towards PM Circulates Online
Executive Summary:
A manipulated image showing someone making an offensive gesture towards Prime Minister Narendra Modi is circulating on social media. However, the original photo does not display any such behavior towards the Prime Minister. The CyberPeace Research Team conducted an analysis and found that the genuine image was published in a Hindustan Times article in May 2019, where no rude gesture was visible. A comparison of the viral and authentic images clearly shows the manipulation. Moreover, The Hitavada also published the same image in 2019. Further investigation revealed that ABPLive also had the image.

Claims:
A picture showing an individual making a derogatory gesture towards Prime Minister Narendra Modi is being widely shared across social media platforms.



Fact Check:
Upon receiving the news, we immediately ran a reverse search of the image and found an article by Hindustan Times, where a similar photo was posted but there was no sign of such obscene gestures shown towards PM Modi.

ABP Live and The Hitavada also have the same image published on their website in May 2019.


Comparing both the viral photo and the photo found on official news websites, we found that almost everything resembles each other except the derogatory sign claimed in the viral image.

With this, we have found that someone took the original image, published in May 2019, and edited it with a disrespectful hand gesture, and which has recently gone viral across social media and has no connection with reality.
Conclusion:
In conclusion, a manipulated picture circulating online showing someone making a rude gesture towards Prime Minister Narendra Modi has been debunked by the Cyberpeace Research team. The viral image is just an edited version of the original image published in 2019. This demonstrates the need for all social media users to check/ verify the information and facts before sharing, to prevent the spread of fake content. Hence the viral image is fake and Misleading.
- Claim: A picture shows someone making a rude gesture towards Prime Minister Narendra Modi
- Claimed on: X, Instagram
- Fact Check: Fake & Misleading
Related Blogs

Executive Summary
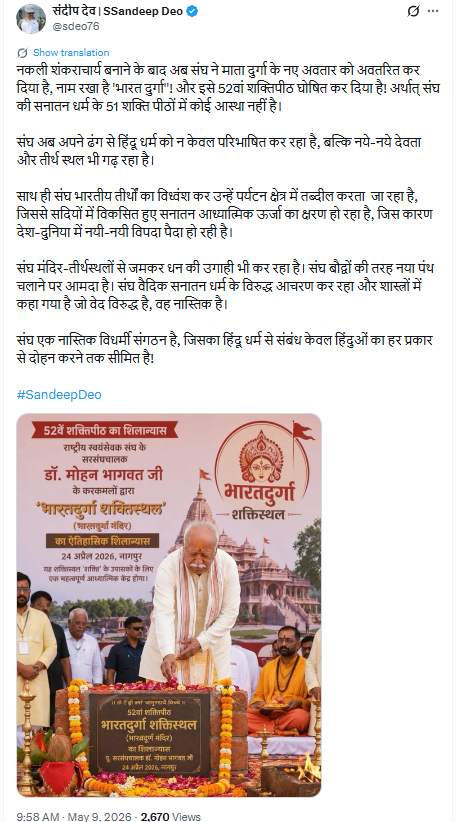
A picture of Mohan Bhagwat is going viral on social media, showing him allegedly laying the foundation stone of a so-called “52nd Shakti Peeth” named Bharatdurga. Users are claiming that the RSS chief insulted Sanatan Dharma by creating a new Shakti Peeth in Nagpur. Research by CyberPeace Research Wing found that the claim is false. The viral image is AI-generated, and Mohan Bhagwat did not inaugurate any “52nd Shakti Peeth.” In reality, he laid the foundation stone of the Bharatdurga Temple.
Claim
An X user named Sandeep Dev shared the viral image and alleged that after creating “fake Shankaracharyas,” the RSS had now introduced a new form of Goddess Durga called “Bharat Durga” and declared it the 52nd Shakti Peeth. The post further claimed that the RSS was redefining Hinduism and creating new religious sites.
Fact Check
To verify the claim, we searched relevant keywords and found reports published on April 24, 2026, by India TV and Navbharat Times. According to these reports, Mohan Bhagwat laid the foundation stone of the world’s first Bharatdurga Temple in Nagpur during a ceremony organized at the Jamtha campus of Dr. Abaji Thatte Seva and Research Institute. Several prominent saints and religious leaders attended the event. Importantly, none of the reports described the temple as the “52nd Shakti Peeth.”


Further research led us to the full video of the foundation ceremony uploaded on the YouTube channel of Devendra Fadnavis. The stage backdrop and video thumbnail clearly mention “Bharatdurga Temple Foundation Ceremony.” However, the viral image frame was not visible anywhere in the authentic footage.

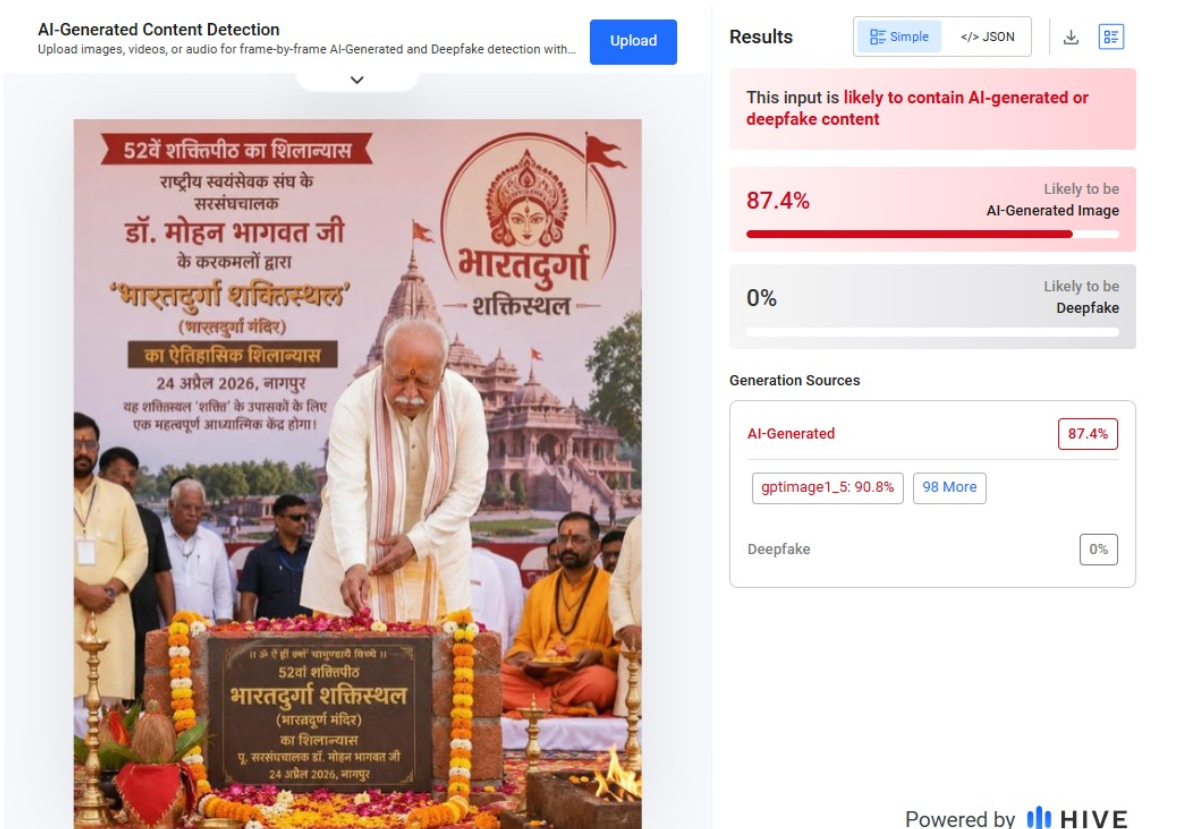
We also analyzed the viral image using AI detection tools, which indicated that the image was AI-generated.
Conclusion
Our research confirms that the claim about Mohan Bhagwat laying the foundation of a “52nd Shakti Peeth” is false. The viral image is AI-generated. In reality, he participated in the foundation ceremony of the Bharatdurga Temple in Nagpur.
Introduction
There has been a recent surge of misinformation all over social media, claiming that every Indian ought to receive an allowance of ₹2,000 under some "Prime Minister's scheme." The message, which has been circulated far and wide on almost all platforms-WhatsApp, Facebook, Telegram, etc.-has urged users to click on an unfamiliar link to claim the allowance in their bank accounts.
It would seem like a very attractive offer, especially at a time when common citizens are coping with rising costs of living. But upon further examination, it turns out to be an outright online scam. NewsMobile fact-checked the claim and confirmed that no such scheme exists. Thus, the message circulating is a scam that aims to mislead common citizens.
Such an incident is not isolated. Over the years, fraudulent posts falsely offering benefits in the name of the government or well-known brands have been on the rise. These scams are not just about misinformation-they take advantage of trust, lure people into clicking, and sharing personal info that poses serious risks to financial and personal security.
Anatomy of the Viral PM Scheme Scam
The viral message received attention and was written in Hindi. It read:
“सभी नागरिकों को PM योजना के तहत दो हज़ार रुपए का भत्ता प्रदान किया गया है अपने bank खाते में प्राप्त करने के लिए click करें."
(English: “All citizens have been provided an allowance of ₹2000 under the PM scheme. Click to receive it in your bank account.”)
Beneath this was an odd link that, upon clicking through investigation, turned out to be not working and invalid. An examination of government sites, official handle accounts, and other such was done and no announcement for any such allowance was found.
This provides a neat explanation of a phishing attempt by which a scammer induces urgency and temptation in order to lure citizens into clicking a malicious link. While the link may no longer be active, it could very well have once redirected users to websites that harvest personal information such as Aadhaar numbers, bank details, or login credentials.
The Broader Problem: Fake Government Scheme Scams
Some scams have been exploiting the hoax gimmick of the ₹2,000 PM scheme into the wider trend. How do the con men work? They leverage the credibility of governmental initiatives to scam citizens. In the past, fake promises were made concerning free gas cylinders, cash allowances, subsidised rations, or even job opportunities.
During the COVID times, for instance, fake vaccination registration links and so-called relief scheme offers went viral, preying on the fears and vulnerabilities of ill-informed citizens. Likewise, false schemes associated with reputed companies such as Amazon, Flipkart, TATA Group, and Hermès have also gone viral, promising free gifts or allowances.
The one thing that makes scams associated with the government very dangerous is the exploitation of people's trust in authority. The common citizen is predisposed to believe the PM scheme or the Government Yojana because of the social credibility accorded to these announcements.
How These Scams Operate
These are scams where the creators intend deception and in the end, gain from defrauding a person. Fraudsters first create clickbait messages that are duly recorded to resemble official communications and often bear the government logos and bear a mix of Hindi-English text with the phrase "Pradhan Mantri Yojana" to make it sound legitimate. The messages then redirect users to bogus websites that really look very much like the government's portals, asking sick persons to enter personal information. Finally, as soon as they have obtained this data, the scammer uses it for identity theft, bank fraud, or sells it on the dark web. Social engineering does play a large role in these scams: here terms of urgency like limited time, last chance, and whatnot get created with the aim of pushing the targets to act on these without thinking. For maximum reach, victims are also asked to forward the message to their friends and family, causing the scammer to go viral across WhatsApp, Facebook, and Telegram.
Risks to Citizens
Risks are serious and manifold to falling prey to these scams. The immediate kind of risk is financial loss: divulging bank account details, an OTP, or credentials may constitute providing attackers the power to drain funds therefrom. Another prevalent kind of identity theft occurs through hijacked Aadhaar, PAN, or personal information that subsequently finds its way into fake loans or SIM activations. Apart from monetary losses, opening malicious links might also make devices infected with spyware or ransomware, thereby invading privacy and security. Victims tend to experience a form of psychological trauma due to feelings of betrayal or humiliation of being deceived, thus discouraging them from reporting, which in turn enables such scams to go undetected.
Best Practices for Prevention
It is prudent to exercise good cyber hygiene and be on the lookout for such scams. The citizens should verify each statement against government-authorised websites like https://www.mygov.in or through press statements of the ministries prior to believing it. One should not click on suspicious links offering money, gifts, or subsidies. Red flags like poor grammar, an unofficial domain name, or too-good-to-be-true offers can enable one to identify the scam in time. Two-factor authentication, antivirus software updates, and securing devices can drastically lower the threat from the technical angle. Equally important is the reporting of issues: always report any suspicious activities to cybercrime.gov.in or to the nearest cyber cell so that the authorities may trace some pattern and issue advisories accordingly. Finally, one can do some good by sharing verified fact checks within their circles to build added strength against misinformation and scams.
Policy and Community Role
While individual awareness is important, collective action must be taken against these fake government scheme scams. Platforms such as WhatsApp, Facebook, and X (Twitter) must tune up fraudsters' message detection mechanisms. In the meantime, Government Bodies must alert citizens periodically on new scams through their official handles/schemes and through community outreach.
Civil society and fact-checking agencies play an important role in dispelling frequently viral hoaxes. This work must be amplified to reach people's consciousness in regional languages for the very reason that in these terrain zones, forwarded messages are much more trusted.
Conclusion
The viral ₹2,000 PM scheme scam is a reminder that everything that is viral online cannot be trusted in toto. The scammers of the day are inventing newer scams to gain trust, spread misinformation, and extort innocent citizens.
The best defence will be awareness and alertness. Citizens must verify any claims through official channels before clicking on a link, sharing their data, or even acting upon it in any way. With proper cyber hygiene and avoiding suspicious messages, we can counterattack by reducing the percentage of impact that these scams may have and collaboratively build a secure digital environment.
As India pushes itself further into a digital ecosystem, both empowering and being resilient to cyber fraud is not a state of individual security, but a national agenda.
References
- https://www.newsmobile.in/nm-fact-checker/fact-check-viral-post-claiming-pm-scheme-offering-rs-2000-allowance-is-a-scam/
- https://timesofindia.indiatimes.com/business/financial-literacy/investing/beware-of-deepfake-scams-fraudsters-using-ai-videos-to-push-schemes-promising-unrealistic-returns-red-flags-to-watch-out-for/articleshow/124085155.cms
- https://www.business-standard.com/finance/personal-finance/invest-rs-21-000-to-earn-rs-20-lakh-monthly-viral-videos-of-fm-are-fake-125082000517_1.html
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2124728

Introduction
Mr Rajeev Chanderashekhar, MoS, Ministry of Electronics and Information Technology, on 09 March 2023, held a stakeholder consultation on the Digital India Bill. This bill will be the successor to the Information technology Act 2000 and provide a set of regulations and laws which will govern cyberspace in times to come. The consultation was held in Bangalore and was the first of many such consultations where the Digital India bill is to be discussed. These public stakeholder consultations will provide direct public feedback to the ministry, and this will help create a safe and secure ecosystem of Indian Cyber Laws.
What is the Digital India Act?
Cyberspace has evolved the fastest as compared to any other industry, and the evolution of the growth cannot be presumed to be stagnant or stuck as we see new technologies and gadgets being invented all across the globe. The ease created by using technology has changed how we live and function. However, bad actors often use these advantages or fruits of technology to wreak havoc upon the nation’s cyberspace. The use of technology is always governed by the application of usage and safeguard policies and laws. As technology is growing exponentially, it is pertinent that we have laws which are in congruence with today’s time and technology. This is keenly addressed by the Digital India Act, which will be the legislation governing Indian Cyberspace in times to come. This was the need of the hour in order to have the judiciary, legislature and law enforcement agencies ahead of the curve when it comes to cyber crimes and laws.
What is the Digital India Bill’s primary goal?
The Digital India Bill’s goal is to guarantee an institutional structure for accountability and that the internet in India is accessible, unhindered by user harm or criminal activity. The law will apply to new technologies, algorithmic social media platforms, artificial intelligence, user risks, the diversity of the internet, and the regulation of intermediaries. The diversity of the internet, user hazards, artificial intelligence, social media platforms, and intermediary regulation are all discussed.
Why is the Digital India Bill necessary?
The number of internet users in the country currently exceeds 760 million; in the upcoming years, this number will reach 1.2 billion. Despite the fact that the internet is useful and promotes connectivity, there are a number of user damages nearby. Thus, it is crucial to enact legislation to set forth new guidelines for individuals’ rights and responsibilities and mention the requirement to gather data.
Major Elements of the Digital India Act
Major Elements of the Digital India Bill, which will eventually become an Act, which will contribute massively towards a safe cyber-ecosystem, some of these elements aim towards the following-
- The legislation attempts to establish an internet regulator.
- Women and Child safety.
- Safe harbour for intermediaries.
- The right of the individual to secure his information and the requirement to utilise personal data for legal purposes provide the main obstacles to data protection or regulation. The law tries to deal with this difficulty.
- A limit will be placed on how far a person’s personal information can be accessed for legal reasons.
- The majority of the bill’s characteristics are contrasted with the EU’s General Data Protection Regulation.
The Way Ahead
As we ride the wave of developments in cyberspace regarding emerging technologies and automated gadgets, it becomes pertinent that the state takes due note of such technologies and the courts take cognisance of offences committed by using technology. Law enforcement agencies must also train police personnel who can effectively and efficiently investigate cybercrime cases. The ministry also released a few bills last year, such as – the Telecommunication Bill, 2022, Intermediary Rules and the Digital Personal Data Protection Bill, 2022, to better address the shortcomings and the issues in cyberspace and how to safeguard the netizens. The Digital India Act will essentially create a synergy between the current bills and the new ones to come in order to create a wholesome, safe and secure Indian cyber ecosystem.
Conclusion
Digital India Bill is necessary to address the challenges of cyberspace, like personal data and privacy, and policies related to online child and women safety to create a and create a modern and comprehensive legal framework that aligns with global standards of cyber laws. The draft of the bill is expected to come out by July. The ministry looks forward to maximising the impact of the bill through such continuous and effective public consultation to understand and fulfil the expectations and requirements of the Indian netizen, thus empowering him/her equivalent to the netizen of a developed country.


