#Factcheck-Allu Arjun visits Shiva temple after success of Pushpa 2? No, image is from 2017
Executive Summary:
Recently, a viral post on social media claiming that actor Allu Arjun visited a Shiva temple to pray in celebration after the success of his film, PUSHPA 2. The post features an image of him visiting the temple. However, an investigation has determined that this photo is from 2017 and does not relate to the film's release.

Claims:
The claim states that Allu Arjun recently visited a Shiva temple to express his thanks for the success of Pushpa 2, featuring a photograph that allegedly captures this moment.

Fact Check:
The image circulating on social media, that Allu Arjun visited a Shiva temple to celebrate the success of Pushpa 2, is misleading.
After conducting a reverse image search, we confirmed that this photograph is from 2017, taken during the actor's visit to the Tirumala Temple for a personal event, well before Pushpa 2 was ever announced. The context has been altered to falsely connect it to the film's success. Additionally, there is no credible evidence or recent reports to support the claim that Allu Arjun visited a temple for this specific reason, making the assertion entirely baseless.

Before sharing viral posts, take a brief moment to verify the facts. Misinformation spreads quickly and it’s far better to rely on trusted fact-checking sources.
Conclusion:
The claim that Allu Arjun visited a Shiva temple to celebrate the success of Pushpa 2 is false. The image circulating is actually from an earlier time. This situation illustrates how misinformation can spread when an old photo is used to construct a misleading story. Before sharing viral posts, take a moment to verify the facts. Misinformation spreads quickly, and it is far better to rely on trusted fact-checking sources.
- Claim: The image claims Allu Arjun visited Shiva temple after Pushpa 2’s success.
- Claimed On: Facebook
- Fact Check: False and Misleading
Related Blogs

Executive Summary:
This report discloses a new cyber threat contributing to the list of threats targeting internet users in the name of "Aarong Ramadan Gifts". The fraudsters are imitating the popular Bangladeshi brand Aarong, which is known for its Bengali ethnic wear and handicrafts, and allure the victims with the offer of exclusive gifts for Ramadan. The moment when users click on the link, they are taken through a fictitious path of quizzes, gift boxes, and social proof, that simply could damage their personal information and system devices. Through knowing how this is done we can educate users to take caution and stop themselves from falling into cyber threats.
False Claim:
The false message accompanied by a link on social media, claims that Aarong, one of the most respected brands in Bangladesh for their exquisite ethnic wear and handicrafts, is providing Ramadan gifts exclusively through online promotion. And while that may be the facade of the scam, its real aim is to lead users to click on harmful links that may end up in their personal data and devices being compromised.

The Deceptive Journey:
- The Landing page starts with a salutation and a catchy photo of Aarong store, and later moves ahead encouraging the visitors to take a part of a short quiz to claim the gift. This is designed for the purpose of creating a false image of authenticity and trustworthiness.
- A certain area at the end of the page looks like a social media comment section, and users are posting the positive impacts the claim has on them. This is one of the techniques to build the image of a solid base of support and many partakers.
- The quiz starts with a few easy questions on how much the user knows about Aarong and their demographics. This data is vital in the development of more complex threats and can be used to address specific targets in the future.
- After the user hits the OK button, the screen displays a matrix of the Gift boxes, and the user then needs to make at least 3 attempts to attain the reward. This is a commonly used approach which allows the scammer to keep users engaged longer and increases the chances of making them comply with the fraudulent scheme.
- The user is instructed to share the campaign on WhatsApp from this point of the campaign, and the user must keep clicking the WhatsApp button until the progress bar is complete. This is a way to both expand and perpetuate the scam, affecting many more users.
- After completing the steps, the user is shown instructions on how to claim the prize.
The Analysis:
- The home page and quiz are structured to maintain a false impression of genuineness and proficiency, thus allowing the victims to partake in the fraudulent design. The compulsion to forward the message in WhatsApp is the way they inspire more and more users and eventually get into the scam.
- The final purpose of the scam could be to obtain personal data from the user and eventually enter their devices, which could lead to a higher risk of cyber threats, such as identity theft, financial theft, or malware installation.
- We have also cross-checked and as of now there is no well established and credible source or any official notification that has confirmed such an offer advertised by Aarong.
- The campaign is hosted on a third party domain instead of the official Website, this raised suspicion. Also the domain has been registered recently.
- The intercepted request revealed a connection to a China-linked analytical service, Baidu in the backend.

- Domain Name: apronicon.top
- Registry Domain ID: D20231130G10001G_13716168-top
- Registrar WHOIS Server: whois.west263[.]com
- Registrar URL: www.west263[.]com
- Updated Date: 2024-02-28T07:21:18Z
- Creation Date: 2023-11-30T03:27:17Z (Recently created)
- Registry Expiry Date: 2024-11-30T03:27:17Z
- Registrar: Chengdu west dimension digital
- Registrant State/Province: Hei Long Jiang
- Registrant Country: CN (China)
- Name Server: amos.ns.cloudflare[.]com
- Name Server: zara.ns.cloudflare[.]com
Note: Cybercriminal used Cloudflare technology to mask the actual IP address of the fraudulent website.
CyberPeace Advisory:
- Do not open those messages received from social platforms in which you think that such messages are suspicious or unsolicited. In the beginning, your own discretion can become your best weapon.
- Falling prey to such scams could compromise your entire system, potentially granting unauthorized access to your microphone, camera, text messages, contacts, pictures, videos, banking applications, and more. Keep your cyber world safe against any attacks.
- Never, in any case, reveal such sensitive data as your login credentials and banking details to entities you haven't validated as reliable ones.
- Before sharing any content or clicking on links within messages, always verify the legitimacy of the source. Protect not only yourself but also those in your digital circle.
- For the sake of the truthfulness of offers and messages, find the official sources and companies directly. Verify the authenticity of alluring offers before taking any action.
Conclusion:
Aarong Ramadan Gift scam is a fraudulent act that takes advantage of the victims' loyalty to a reputable brand. The realization of the mechanism used to make the campaign look real, can actually help us become more conscious and take measures to our community not to be inattentive against cyberthreats. Be aware, check the credibility, and spread awareness to others wherever you can, to contribute in building a security conscious digital space.
Executive Summary
A video circulating on social media claims that during a summit in Beijing, Donald Trump was seen peeking into Chinese President Xi Jinping’s “private notebook” while Xi briefly stepped away. However, a fact-check by CyberPeace Research Wing found the claim to be baseless. A review of the full event footage clearly shows that the folder in question belonged to Donald Trump himself, not Xi Jinping. The viral interpretation is therefore misleading.
Claim
An X user shared the clip alleging, “Trump caught sneaking a peek at Xi Jinping’s private notebook during a Beijing banquet while Xi stepped away.”

Fact Check
A longer version of the video, shared by NBC News on May 14, shows the state banquet held at the Great Hall of the People in Beijing. Around the 1-minute-50-second mark, Xi Jinping, seated to Trump’s left, gets up and walks to the podium. The viral clip follows shortly after, showing Trump opening the folder placed to his left and flipping through its pages.


The White House also uploaded the full footage on its official YouTube channel, showing wider, uninterrupted shots of the event. Around the two-minute mark, the announcer says, “And now a toast by President Xi,” after which Xi Jinping stands up. Immediately after, Trump is seen opening the folder on his left and reading from it.
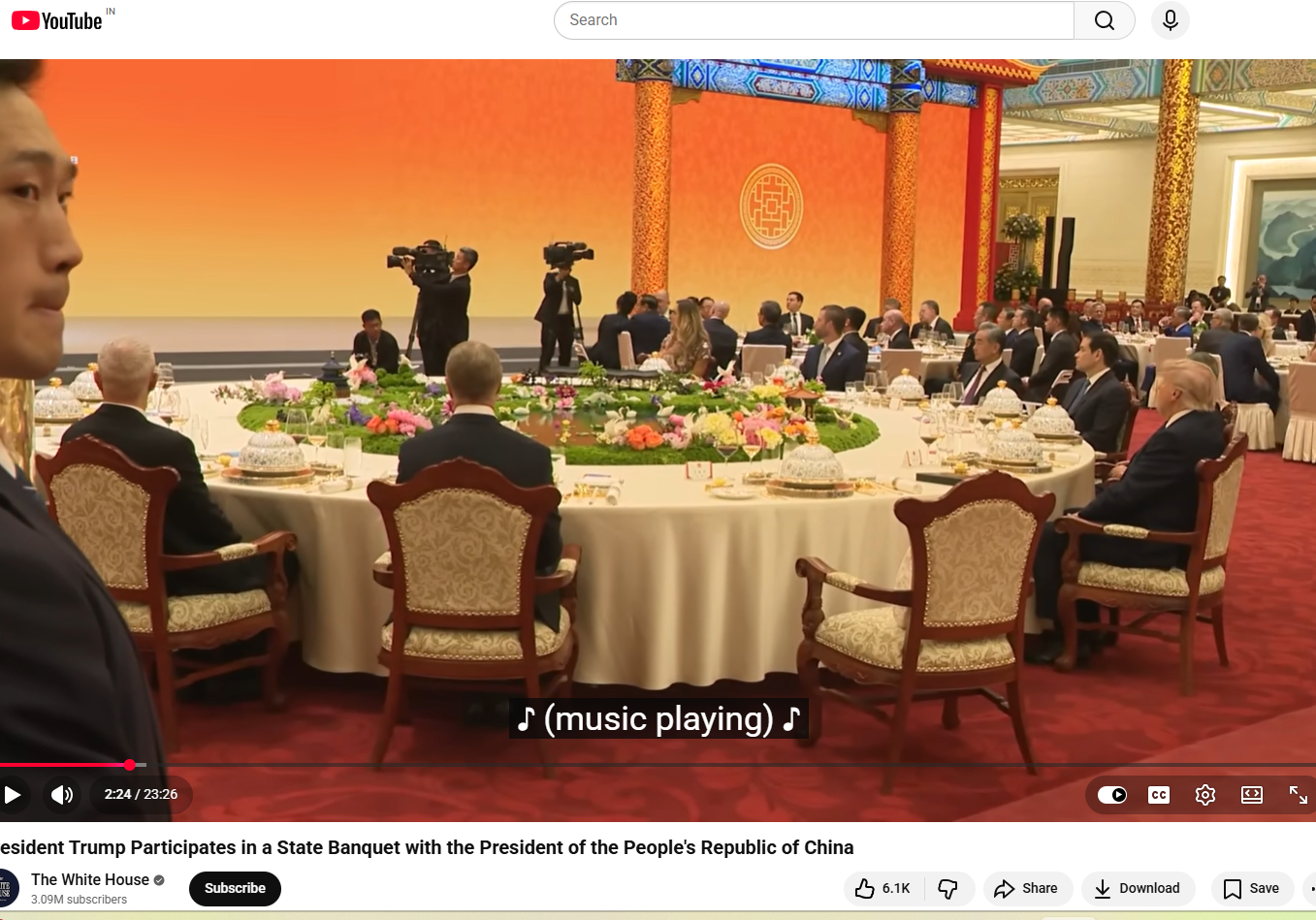
Later in the video, around the 12-minute mark, when Xi returns to his seat, Trump is seen standing up, taking the folder with him to the podium, turning pages, and reading from it. The same sequence can also be seen in the NBC News footage at around 11 minutes and 50 seconds. This clearly indicates that the folder belonged to the U.S. President and not Xi Jinping, and that Trump was not peeking into any private notebook. Another key detail is the embossed emblem on the folder, which closely resembles the Seal of the President of the United States. The American bald eagle, the national bird of the United States, is clearly visible at the centre. A comparison between the viral screenshot and the official seal shows they are nearly identical.
Conclusion
The viral claim is misleading and taken out of context. A detailed review of the full footage, including official recordings from NBC News and the White House, clearly shows that the folder in question belonged to Donald Trump and not Chinese President Xi Jinping. At multiple points in the video, Trump is seen opening, handling, and reading from the same folder, including while Xi Jinping is away from his seat and later after he returns. The visual evidence from the event also supports this conclusion. The embossed seal on the folder matches the official Seal of the President of the United States, further confirming that it was part of Trump’s official briefing material and not any private document belonging to Xi Jinping. Taken together, the full sequence of events and official video sources make it clear that the viral narrative has been incorrectly framed. There is no evidence to suggest that Trump was peeking into Xi Jinping’s personal notebook.

Introduction:
Former Egyptian MP Ahmed Eltantawy was targeted with Cytrox’s predator spyware through links sent via SMS and WhatsApp. Former Egyptian MP Ahmed Eltantawy has been targeted with Cytrox’s Predator spyware in a campaign believed to be state-sponsored cyber espionage. After Eltantawy made his intention to run for president in the 2024 elections known, the targeting took place between May and September 2023. The spyware was distributed using links sent via SMS and WhatsApp, network injection, and visits to certain websites by Eltantawy. The Citizen Lab examined the assaults with the help of Google's Threat Analysis Group (TAG), and they were able to acquire an iPhone zero-day exploit chain that was designed to be used to install spyware on iOS versions up to 16.6.1.
Investigation: The Ahmed Eltantawy Incident
Eltantawy's device was forensically examined by The Citizen Lab, which uncovered several efforts to use Cytrox's Predator spyware to target him. In the investigation, The Citizen Lab and TAG discovered an iOS exploit chain utilised in the attacks against Eltantawy. They started a responsible disclosure procedure with Apple, and as a consequence, it resulted in the release of updates patching the vulnerabilities used by the exploit chain. Mobile zero-day exploit chains may be quite expensive, with black market values for them exceeding millions of dollars. The Citizen Lab also identified several domain names and IP addresses associated with Cytrox’s Predator spyware. Additionally, a network injection method was also utilised to get the malware onto Eltantawy's phone, according to the study. He would be discreetly routed to a malicious website using network injection when he went to certain websites that weren't HTTPS.
What is Cyber Espionage?
Cyber espionage, also referred to as cyber spying, is a sort of cyberattack in which an unauthorised user tries to obtain confidential or sensitive information or intellectual property (IP) for financial gain, business benefit, or political objectives.
Apple's Response: A Look at iOS Vulnerability Patching
Users are advised to keep their devices up-to-date and enable lockdown Mode on iPhones. Former Egyptian MP targeted with predator spyware ahead of 2024 presidential run hence Update your macOS Ventura, iOS, and iPadOS devices, as Apple has released emergency updates to address the flaws. Apple has Released Emergency Updates Amid Citizen Lab’s Disclosure. Apple has issued three emergency updates for iOS, iPadOS (1), and macOS Ventura (2).
The updates address the following vulnerabilities:
CVE-2023-41991,
CVE-2023-41992,
CVE-2023-41993.
Apple customers are advised to immediately install these emergency security updates to protect themselves against potential targeted spyware attacks. By updating promptly, users will ensure that their devices are secure and cannot be compromised by such attacks exploiting these particular zero-day vulnerabilities. Hence it is advisable to maintain up-to-date software and enable security features in your Apple devices.
Conclusion:
Ahmed Eltantawy, a former Egyptian MP and presidential candidate, was targeted with Cytrox’s Predator spyware after announcing his bid for the presidency. He was targeted by Cytrox Predator Spyware Campaign. Such an incident is believed to be State-Sponsored Cyber Espionage. The incident raises the question of loss of privacy and shows the mala fide intention of the political opponents. The investigation Findings reveal that Ahmed Eltantawy was the victim of a sophisticated cyber espionage campaign that leveraged Cytrox’s Predator spyware. Apple advised that all users are urged to update their Apple devices. This case raises alarming concerns about the lack of controls on the export of spyware technologies and underscores the importance of security updates and lockdown modes on Apple devices.
References:
- https://uksnackattack.co.uk/predator-in-the-wires-ahmed-eltantawy-targeted-by-predator-spyware-upon-presidential-ambitions-announcement
- https://citizenlab.ca/2023/09/predator-in-the-wires-ahmed-eltantawy-targeted-with-predator-spyware-after-announcing-presidential-ambitions/#:~:text=Between%20May%20and%20September%202023,in%20the%202024%20Egyptian%20elections.
- https://thehackernews.com/2023/09/latest-apple-zero-days-used-to-hack.html
- https://www.hackread.com/zero-day-ios-exploit-chain-predator-spyware/


