#FactCheck -Viral Image of ‘Saudi Son’ Meeting Hindu Mother Found to Be Misleading
Executive Summary
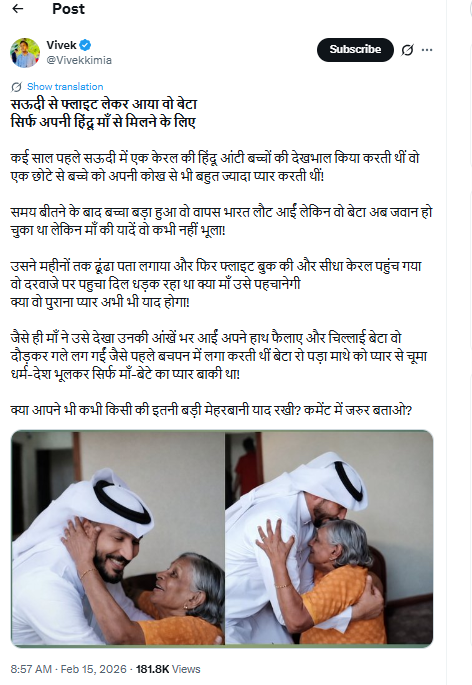
A photo is going viral on social media showing a young man dressed in traditional Arab attire warmly embracing an elderly woman. The post claims that the man flew in from Saudi Arabia to Kerala just to meet his “Hindu mother,” portraying the image as a heartwarming example of communal harmony. However, research by the CyberPeace found that the claim being shared with the image is misleading.
Claim
The viral post narrates an emotional story, alleging that years ago a Hindu woman from Kerala worked in Saudi Arabia caring for children and loved a young boy like her own son. After she returned to India, the boy—now grown up—reportedly searched for her for months, booked a flight, and finally reached Kerala to reunite with her. The post describes an emotional reunion filled with tears, affection, and a bond beyond religion and nationality.
Fact Check
A reverse image search of the viral picture led us to a video uploaded on August 18, 2023, on the YouTube channel of social media influencer Hashim Abbas. In the video, he is seen meeting and hugging the elderly woman while extending Onam greetings.
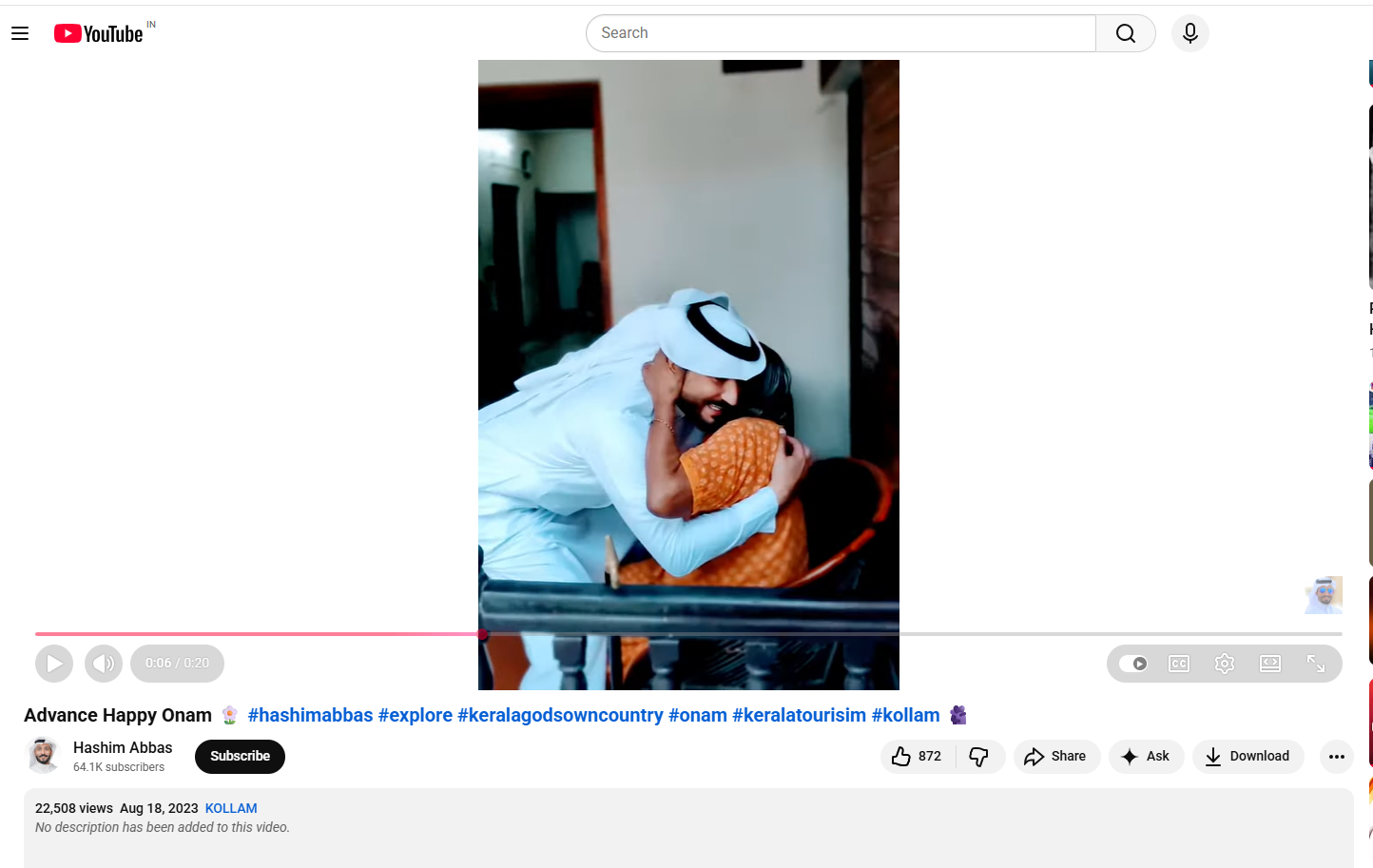
Further examination of Hashim Abbas’ social media accounts revealed several other videos from his Kerala visit. Our research also found that Abbas played a significant role in the Malayalam film Kondotty Pooram.
Additionally, we found a video posted on August 13, 2023, by actress and theatre artist Sandhya Rajendran, daughter of veteran Malayalam actress Vijayakumari. The video shows Vijayakumari teaching Onam songs to Hashim Abbas.

Conclusion
The evidence clearly establishes that the viral claim is misleading. The man seen in the image is Hashim Abbas, who was meeting senior Malayalam actress Vijayakumari to extend Onam greetings. The emotional story about a son flying from Saudi Arabia to reunite with his Hindu mother is fictional and not connected to the viral image.
Related Blogs
.webp)
The Equitable Growth Approach of AI and Digital Twins
Digital Twins can be simply described as virtual replicas of physical assets or systems, powered by real-time data and advanced simulations. When this technology is combined with AI, the impact it has on enabling real-time monitoring, predictive maintenance, optimised operations, and improved design processes through the creation of virtual replicas of physical assets becomes even greater. The greatest value of AI is its ability to make data actionable. And when combined with digital twins, these data can be collated, analysed, inefficiencies removed, and better decisions can be taken to improve efficiency and quality.
This intersection between AI and Digital Twins holds immense potential for addressing key challenges, particularly in countries like India, which is rapidly embracing digital adoption to achieve its economic ambitions and sustainability goals. According to Salesforce’s most recent survey on generative AI use among the general population within the U.S., UK, Australia and India, 75% of generative AI users are looking to automate repetitive tasks and use generative AI for work communications. India is particularly looking towards a rapid digital adoption, economic ambitions, and sustainable developments to be achieved through AI adoption. This blog discuss the intersection of equitable growth, sustainability, and AI-driven policies in India.
Sustainability and the Path Ahead: Digital Twin and AI-Driven Solutions
India faces sustainability challenges which are mainly associated with issues such as urban congestion, the rising demand for energy along with climate change and environmental degradation. AI and Digital Twins provide solutions for real-time simulations and predictive analysis. Some of the examples are its applications in sustainable urban planning such as smart cities like the Indore Smart City Initiative and traffic optimisation, energy efficiency/optimisation through AI-driven renewable energy projects and power grid optimisation and even water resource management through leak detection, equitable distribution and conservation.
The need is to balance innovation with regulation, particularly, underscoring the importance of ethical and sustainable deployment of AI and digital twins and addressing data privacy with AI ethics with recent developments such as the India’s evolving AI policy landscape, including the National Strategy for Artificial Intelligence and its focus on AI for All, regulatory frameworks such as DPDP Act and the manner in which they address AI ethics, data privacy, and digital governance.
The need is to initiate targeted policies that promote research and development in AI and digital twin technologies, skill development and partnerships with the private sector, think tanks, nonprofits and others. Also, collaborations at the global level would include aligning our domestic policies with global AI and sustainability initiatives and leveraging the international frameworks for climate tech and smart infrastructure.
Cyberpeace Outlook
As part of specific actions, policymakers need to engage in proactive governance to ensure the responsible use and development of AI. This includes enacting incentive schemes for sustainable AI projects and strengthening the enforcement of data privacy laws. Industry leaders must support equitable access to AI and digital twin technologies and develop tailored AI tools for resource-constrained settings, particularly in India. Finally, researchers need to drive innovation in alignment with sustainability goals, such as those related to agriculture and groundwater management.
References
- https://economictimes.indiatimes.com/tech/artificial-intelligence/technologies-like-ai-and-digital-twins-can-tackle-challenges-like-equitable-growth-to-sustainability-wef/articleshow/117121897.cms
- https://www.salesforce.com/news/stories/generative-ai-statistics/
- https://www.mdpi.com/2673-2688/4/3/38
- https://www.ibm.com/think/topics/generative-ai-for-digital-twin-energy-utilities

Introduction
The Information Technology (IT) Ministry has tested a new parental control app called ‘SafeNet’ that is intended to be pre-installed in all mobile phones, laptops and personal computers (PCs). The government's approach shows collaborative efforts by involving cooperation between Internet service providers (ISPs), the Department of School Education, and technology manufacturers to address online safety concerns. Campaigns and the proposed SafeNet application aim to educate parents about available resources for online protection and safeguarding their children.
The Need for SafeNet App
SafeNet Trusted Access is an access management and authentication service that ensures no user is a target by allowing you to expand authentication to all users and apps with diverse authentication capabilities. SafeNet is, therefore, an arsenal of tools, each meticulously crafted to empower guardians in the art of digital parenting. With the finesse of a master weaver, it intertwines content filtering with the vigilant monitoring of live locations, casting a protective net over the vulnerable online experiences of the children. The ability to oversee calls and messages adds another layer of security, akin to a watchful sentinel standing guard over the gates of communication. Some pointers regarding the parental control app that can be taken into consideration are as follows.
1. Easy to use and set up: The app should be useful, intuitive, and easy to use. The interface plays a significant role in achieving this goal. The setup process should be simple enough for parents to access the app without any technical issues. Parents should be able to modify settings and monitor their children's activity with ease.
2. Privacy and data protection: Considering the sensitive nature of children's data, strong privacy and data protection measures are paramount. From the app’s point of view, strict privacy standards include encryption protocols, secure data storage practices, and transparent data handling policies with the right of erasure to protect and safeguard the children's personal information from unauthorized access.
3. Features for Time Management: Effective parental control applications frequently include capabilities for regulating screen time and establishing use limitations. The app will evaluate if the software enables parents to set time limits for certain applications or devices, therefore promoting good digital habits and preventing excessive screen time.
4. Comprehensive Features of SafeNet: The app's commitment to addressing the multifaceted aspects of online safety is reflected in its robust features. It allows parents to set content filters with surgical precision, manage the time their children spend in the digital world, and block content that is deemed age-inappropriate. This reflects a deep understanding of the digital ecosystem's complexities and the varied threats that lurk within its shadows.
5. Adaptable to the needs of the family: In a stroke of ingenuity, SafeNet offers both parent and child versions of the app for shared devices. This adaptability to diverse family dynamics is not just a nod to inclusivity but a strategic move that enhances its usability and effectiveness in real-world scenarios. It acknowledges the unique tapestry of family structures and the need for tools that are as flexible and dynamic as the families they serve.
6. Strong Support From Government: The initiative enjoys a chorus of support from both government and industry stakeholders, a symphony of collaboration that underscores the collective commitment to the cause. Recommendations for the pre-installation of SafeNet on devices by an industry consortium resonate with the directives from the Prime Minister's Office (PMO),creating a harmonious blend of policy and practice. The involvement of major telecommunications players and Internet service providers underscores the industry's recognition of the importance of such initiatives, emphasising a collaborative approach towards deploying digital safeguarding measures at scale.
Recommendations
The efforts by the government to implement parental controls a recommendable as they align with societal goals of child welfare and protection. This includes providing parents with tools to manage and monitor their children's Internet usage to address concerns about inappropriate content and online risks. The following suggestions are made to further support the government's initiative:
1. The administration can consider creating a verification mechanism similar to how identities are verified when mobile SIMS are issued. While this certainly makes for a longer process, it will help address concerns about the app being misused for stalking and surveillance if it is made available to everyone as a default on all digital devices.
2. Parental controls are available on several platforms and are designed to shield, not fetter. Finding the right balance between protection and allowing for creative exploration is thus crucial to ensuring children develop healthy digital habits while fostering their curiosity and learning potential. It might be helpful to the administration to establish updated policies that prioritise the privacy-protection rights of children so that there is a clear mandate on how and to what extent the app is to be used.
3. Policy reforms can be further supported through workshops, informational campaigns, and resources that educate parents and children about the proper use of the app, the concept of informed consent, and the importance of developing healthy, transparent communication between parents and children.
Conclusion
Safety is a significant step towards child protection and development. Children have to rely on adults for protection and cannot identify or sidestep risk. In this context, the United Nations Convention on the Rights of the Child emphasises the matter of protection efforts for children, which notes that children have the "right to protection". Therefore, the parental safety app will lead to significant concentration on the general well-being and health of the children besides preventing drug misuse. On the whole, while technological solutions can be helpful, one also needs to focus on educating people on digital safety, responsible Internet use, and parental supervision.
References
- https://www.hindustantimes.com/india-news/itministry-tests-parental-control-app-progress-to-be-reviewed-today-101710702452265.html
- https://www.htsyndication.com/ht-mumbai/article/it-ministry-tests-parental-control-app%2C-progress-to-be-reviewed-today/80062127
- https://www.varindia.com/news/it-ministry-to-evaluate-parental-control-software
- https://www.medianama.com/2024/03/223-indian-government-to-incorporate-parental-controls-in-data-usage/

Executive Summary:
A viral post on X (formerly Twitter) gained much attention, creating a false narrative of recent damage caused by the earthquake in Tibet. Our findings confirmed that the clip was not filmed in Tibet, instead it came from an earthquake that occurred in Japan in the past. The origin of the claim is traced in this report. More to this, analysis and verified findings regarding the evidence have been put in place for further clarification of the misinformation around the video.

Claim:
The viral video shows collapsed infrastructure and significant destruction, with the caption or claims suggesting it is evidence of a recent earthquake in Tibet. Similar claims can be found here and here

Fact Check:
The widely circulated clip, initially claimed to depict the aftermath of the most recent earthquake in Tibet, has been rigorously analyzed and proven to be misattributed. A reverse image search based on the Keyframes of the claimed video revealed that the footage originated from a devastating earthquake in Japan in the past. According to an article published by a Japanese news website, the incident occurred in February 2024. The video was authenticated by news agencies, as it accurately depicted the scenes of destruction reported during that event.

Moreover, the same video was already uploaded on a YouTube channel, which proves that the video was not recent. The architecture, the signboards written in Japanese script, and the vehicles appearing in the video also prove that the footage belongs to Japan, not Tibet. The video shows news from Japan that occurred in the past, proving the video was shared with different context to spread false information.

The video was uploaded on February 2nd, 2024.
Snap from viral video

Snap from Youtube video

Conclusion:
The video viral about the earthquake recently experienced by Tibet is, therefore, wrong as it appears to be old footage from Japan, a previous earthquake experienced by this nation. Thus, the need for information verification, such that doing this helps the spreading of true information to avoid giving false data.
- Claim: A viral video claims to show recent earthquake destruction in Tibet.
- Claimed On: X (Formerly Known As Twitter)
- Fact Check: False and Misleading


