#FactCheck-RBI's Alleged Guidelines on Ink Colour for Cheque Writing
Executive Summary:
A viral message is circulating claiming the Reserve Bank of India (RBI) has banned the use of black ink for writing cheques. This information is incorrect. The RBI has not issued any such directive, and cheques written in black ink remain valid and acceptable.

Claim:
The Reserve Bank of India (RBI) has issued new guidelines prohibiting using black ink for writing cheques. As per the claimed directive, cheques must now be written exclusively in blue or green ink.

Fact Check:
Upon thorough verification, it has been confirmed that the claim regarding the Reserve Bank of India (RBI) issuing a directive banning the use of black ink for writing cheques is entirely false. No such notification, guideline, or instruction has been released by the RBI in this regard. Cheques written in black ink remain valid, and the public is advised to disregard such unverified messages and rely only on official communications for accurate information.
As stated by the Press Information Bureau (PIB), this claim is false The Reserve Bank of India has not prescribed specific ink colors to be used for writing cheques. There is a mention of the color of ink to be used in point number 8, which discusses the care customers should take while writing cheques.


Conclusion:
The claim that the Reserve Bank of India has banned the use of black ink for writing cheques is completely false. No such directive, rule, or guideline has been issued by the RBI. Cheques written in black ink are valid and acceptable. The RBI has not prescribed any specific ink color for writing cheques, and the public is advised to disregard unverified messages. While general precautions for filling out cheques are mentioned in RBI advisories, there is no restriction on the color of the ink. Always refer to official sources for accurate information.
- Claim: The new RBI ink guidelines are mandatory from a specified date.
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Introduction
Embark on a groundbreaking exploration of the Darkweb Metaverse, a revolutionary fusion of the enigmatic dark web with the immersive realm of the metaverse. Unveiling a decentralised platform championing freedom of speech, the Darkverse promises unparalleled diversity of expression. However, as we delve into this digital frontier, we must tread cautiously, acknowledging the security risks and societal challenges that accompany the metaverse's emergence.
The Dark Metaverse is a unique combination of the mysterious dark web and the immersive digital world known as the metaverse. Imagine a place where users may participate in decentralised social networking, communicate anonymously, and freely express a range of viewpoints. It aims to provide an alternative to traditional online platforms, emphasizing privacy and freedom of speech. Nevertheless, it also brings new kinds of criminality and security issues, so it's important to approach this digital frontier cautiously.
In the vast expanse of the digital cosmos, there exists a realm that remains shrouded in mystery to the casual netizen—the dark web. It is a place where the surface web, the familiar territory of Google searches and social media feeds, constitutes a mere 5 per cent of the information iceberg floating in an ocean of data. Beneath this surface lies the deep web and the dark web, comprising the remaining 95 per cent, a staggering figure that beckons the brave and curious to explore its abysmal depths.
Imagine, a platform that not only ventures into these depths but intertwines them with the emerging concept of the metaverse—a digital realm that defeats the limitations of the physical world. This is the vision of the Darkweb Metaverse, the world’s premier endeavour to harness the enigmatic depths of the dark web and fuse it into the immersive experience of the metaverse.
As per Internet User Statistics 2024, There are over 5.3 billion Internet users in the world, meaning over 65% of the world’s population has access to the Internet. The Internet is used for various services. News, entertainment, and communication to name a few. The citizens of developed countries depend on the World Wide Web for a multitude of daily tasks such as academic research, online shopping, E-banking, accessing news and even ordering food online hence the Internet has become an integral part of our daily lives.
Surface Web
This layer of the internet is used by the general public on a daily basis. The contents of this layer are accessed by standard web browsers namely Google Chrome, and Mozilla Firefox to name a few. The contents of this layer of the internet are indexed by these search engines.
Deep Web
This is the second layer of the internet; its contents are not indexed by search engines. The content that is unavailable on the surface web is considered to be a part of the deep web. The deep web comprises a collection of various types of confidential information. Several Schools, Universities, Institutes, Government Offices and Departments, Multinational Companies (MNCs), and Private Companies store their database information and website-oriented server information such as online profile and accounts usernames or IDs and passwords or log in credentials and companies' premium subscription data and monetary transactional records in the Intra-net which is part of the deep web.
Dark Web
It is the least explored part of the internet which is considered to be a hub of various bizarre activities. The contents of the dark web are not indexed by search engines and specific software is required to access this layer of the internet namely TOR (The Onion Router) browser which cloaks to identify its users making them anonymous. The websites of the dark web are identified from .onion TLD (Top Level Domain). Due to anonymity provided in this layer, various criminal activities take place over there including Drugs trading, Arms trading, and Illegal PayPal account details to websites offering child pornography.
The Darkverse
The Darkweb Metaverse is not a mere novelty; it is a revolutionary step forward, a decentralised social networking platform that stands in stark contrast to centralised counterparts like YouTube or Twitter. Here, the spectre of censorship is banished, and the freedom of speech reigns supreme.
The architectonic prowess behind the Darkweb Metaverse is formidable. The development team is a coalition of former infrastructure maestros from Theta Network and virtuosos of metaverse design, bolstered by backend engineers from Gensokishi Metaverse. At the helm is a CEO whose tenure at the apex of large Japanese companies has endowed him with a profound understanding of the landscape, setting a solid foundation for the platform's future triumphs.
Financially, the dark web has been a flourishing underworld, with revenues ranging from $1.5 billion to $3.1 billion between 2020 and 2022. Darkverse, with its emphasis on user-friendliness and safety, is poised to capture a significant portion of this user base. The platform serves as a truly decentralised amalgamation of the Dark Web, Metaverse, and Social Networking Services (SNS), with a mission to provide an unassailable bastion for freedom of speech and expression.
The Darkweb Metaverse is not merely a sanctuary for anonymity and privacy; it is a crucible for the diversity of expression. In a world where centralised platforms can muzzle voices, Darkverse stands as a bulwark against such suppression, fostering a community where a kaleidoscope of opinions and information thrives. The ease of use is unparalleled—a one-time portal that obviates the need for third-party software to access the dark web, protecting users from the myriad risks that typically accompany such ventures.
Moreover, the platform's ability to verify the authenticity of information is a game-changer. In an era laced with misinformation, especially surrounding contentious issues like war, Darkverse offers a sign of truth where the source of information can be scrutinised for its accuracy.
Integrating Technologies
The metaverse will be an immersive iteration of the internet, decked with interactive features of emerging technologies such as artificial intelligence, virtual and augmented reality, 3D graphics, 5G, holograms, NFTs, blockchain and haptic sensors. Each building block, while innovative, carries its own set of risks—vulnerabilities and design flaws that could pose a serious threat to the integrated meta world.
The dark web's very nature of interaction through avatars makes it a perfect candidate for a metaverse iteration. Here, in this anonymous world, commercial and personal engagements occur without the desire to unveil real identities. The metaverse's DNA is well-suited to the dark web, presenting a formidable security challenge as it is likely to evolve more rapidly than its real-world counterpart.
While Meta (formerly Facebook) is a prominent entity developing the metaverse, other key players include NVIDIA, Epic Games, Microsoft, Apple, Decentraland, Roblox Corporation, Unity Software, Snapchat, and Amazon. These companies are integral to constructing the vast network of real-time 3D virtual worlds where users maintain their identities and payment histories.
Yet, with innovation comes risk. The metaverse will necessitate police stations, not as a dystopian oversight but as a means to address the inherent challenges of a new digital society. In India, for instance, the integration of law enforcement within the metaverse could revolutionize the public's interaction with the police, potentially increasing the reporting of crimes.
The Perils within the Darkverse
The metaverse will also be a fertile ground for crimes of a new dimension—identity theft, digital asset hijacking, and the influence of metaverse interactions on real-world decisions. With a significant portion of social media profiles potentially being fraudulent, the metaverse amplifies these challenges, necessitating robust identity access management.
The integration of NFTs into the metaverse ecosystem is not without its security concerns, as token breaches and hacks remain a persistent threat. The metaverse's parallel economy will test the developers' ability to engender trust, a Herculean task that will challenge the boundaries of national economies.
Moreover, the metaverse will be a crucible for social engineering-based attacks, where the real-time and immersive nature of interactions could make individuals particularly vulnerable to deception and manipulation. The potential for early-stage fraud, such as the hyping and selling of virtual assets at unrealistic prices, is a stark reality.
The metaverse also presents numerous risks, particularly for children and adolescents who may struggle to distinguish between virtual and real worlds. The implications of such immersive experiences are intense, with the potential to influence behaviour in hazardous ways.
Security risks extend to the technologies supporting the metaverse, such as virtual and augmented reality. The exploitation of biometric data, the bridging of virtual and real worlds, and the tendency for polarisation and societal isolation are all issues requiring immediate attention.
A Way Forward
As we stand on the cusp of this new digital frontier, it is evident that the metaverse, despite its reliance on blockchain, is not immune to the privacy and security breaches that have plagued conventional IT infrastructure. Data security, Identity theft, network security, and ransomware attacks are just a few of the challenges on the way.
In this quest into the unknown, the Darkweb Metaverse radiates with the promise of freedom and the thrill of discovery. Yet, as we navigate these shadowy depths, we must remain vigilant, for the very technologies that empower us also rear the seeds of our grim vulnerabilities. The metaverse is not just a new chapter in the story of the internet—it is a whole narrative, one that we must write with caution and care.
References
- https://spores.medium.com/the-worlds-first-platform-to-deploy-the-dark-web-in-the-metaverse-releap-ido-on-spores-launchpad-a36387b184de
- https://www.makeuseof.com/how-hackers-sell-trade-data-in-metaverse/
- https://www.demandsage.com/internet-user-statistics/#:~:text=There%20are%20over%205.3%20billion,has%20access%20to%20the%20Internet.
Executive Summary
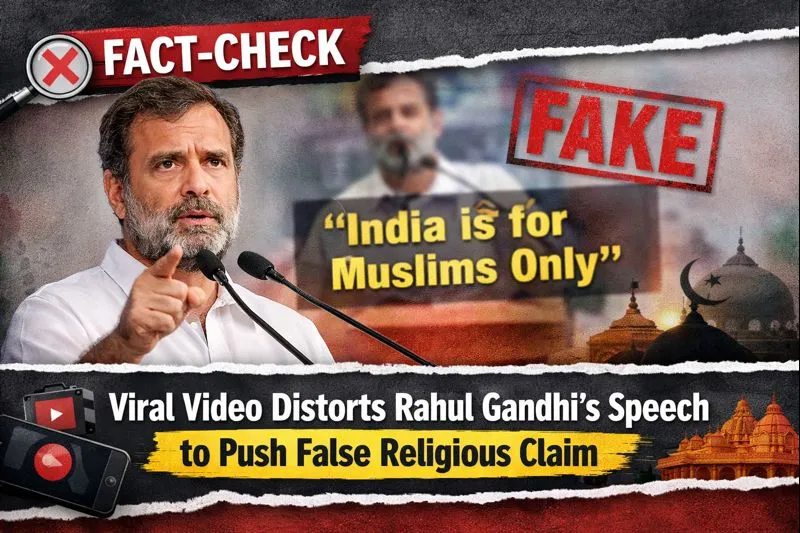
A video of the Leader of the Opposition in the Lok Sabha and Congress MP Rahul Gandhi is being widely shared on social media. In the clip, Gandhi is seen saying that he does not know what “G Gram G” is. Several users are sharing the video with the claim that Rahul Gandhi insulted Lord Ram. However, CyberPeace research found that the claim is misleading. Rahul Gandhi was not referring to Lord Ram in the video. Instead, he was speaking about a newly introduced law titled Viksit Bharat–G RAM G (VB–G RAM G), which has been brought in to replace the Mahatma Gandhi National Rural Employment Guarantee Act (MGNREGA). The viral clip has been shared with a false narrative.
Claim
On January 22, 2026, an Instagram user apnisarkar2024 shared the video claiming, “Rahul Gandhi once again insulted Shri Ram.” (Link, archive link, and screenshot available above)
- https://www.instagram.com/reel/DTzeiy0k3l5
- https://perma.cc/J3A3-NGBM?type=standard

Research
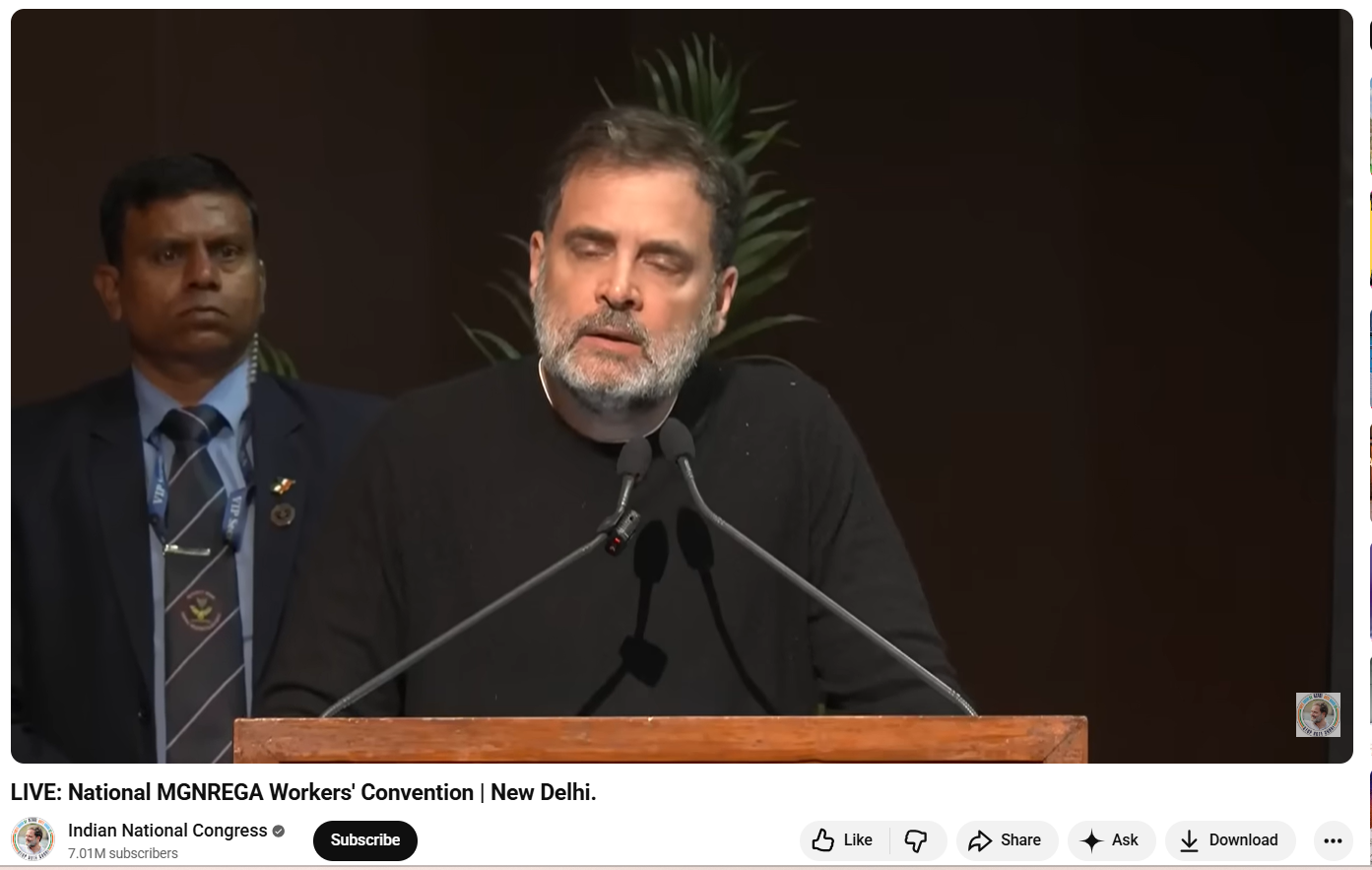
As part of the Research, we first closely examined the viral video. In the clip, Rahul Gandhi is heard saying: “I don’t know what Gram G is. I don’t even know the name of this new law… what is G Gram G…” At no point in the video does Rahul Gandhi mention Lord Ram or make any comment related to religion. To verify the context, we extracted keyframes from the viral clip and conducted a Google Lens search. This led us to a longer version of the same speech uploaded on the official YouTube channel of the Indian National Congress on January 22, 2026. The viral segment appears after the 39:50-minute mark.
The video is from the National MGNREGA Convention held in New Delhi, where Rahul Gandhi criticised the central government over the replacement of MGNREGA with the new VB–G RAM G law. During his speech, he expressed his opposition to the new legislation and stated that he was unfamiliar with its details. Throughout the address, he did not mention or refer to Lord Ram in any manner.
Conclusion
Rahul Gandhi’s remarks in the viral video were related to the newly introduced VB–G RAM G law and were part of his criticism of the central government’s policy decisions. He did not insult Lord Ram. The video is being shared on social media with a misleading and false claim.

Introduction
The debate between free speech and social responsibility is one of the oldest, long-running debates in history. Free speech is considered to be at the heart of every democracy. It is considered the “mother” of all other freedoms, enshrined in Article 19(1)(a) of the Indian Constitution under Part III: Fundamental Rights. It takes various shapes and forms according to the sociopolitical context of society. Evelyn Beatrice Hall, a prominent English writer of the 19th century, laid the foundation of every democracy when she wrote in her book, "I disapprove of what you say, but I willdefend to the death your right to say it." The drastic misuse of social media to disseminate propaganda and fakenews makes it a marketplace of half-baked truth, becoming the antithesis ofwhat early philosophers dreamed of for a democratic modern age. Losethe ethics, and there you have it, the modern conceptualisation of freedom ofspeech and expression in the digital age. The right to freedom of speech andexpression is one of the most fundamental rights, but its exercise is notunfettered, and certain limits are placed upon this right under Art. 19 (2).Every right comes with a corresponding duty, and the exercise of such freedomalso puts the citizenry under the responsibility not to violate the rights ofothers and not to use the media to demean any other person.
SocialMedia: The New Public Square or a Weaponised Echo Chamber
InIndia, Art. 19(1)(a) of the constitution guarantees the right to freedom ofspeech and expression, but it is not absolute. Under Art. 19(2), this right issubject to reasonable restrictions in the interest of public order, decency,morality, and national security. This is construed as a freedom for everyindividual to freely express their opinions, but not to incite violence, spreadfalsehoods, or harm others’ dignity. Unfortunately, the boundaries betweenthese are increasingly blurred.
Thedissemination of unfiltered media and the strangulation of innocence by pushingoften vulgar and obscene content down the throats of individuals, withoutverifying the age and gender profile of the social media user, is a big farcein the name of free speech and a conscious attempt by the intermediaries andsocial media platforms such as Facebook, Instagram, Threads, etc., to wriggleout of their responsibility. A prime example is when Meta’s Mark Zuckerberg, on7th January 2025, gave a statement asserting less intervention into what peoplefind on its social media platforms as the new “best practice”. While lessinterference would have worked in a generation that merely operated on thediffering, dissenting, and raw ideas bred by the minds of differentindividuals, it is not the case for this day and age. There has been asignificant rise in cases where social media platforms have been used as abattleground for disputes, spreading communal violence, misinformation, anddisinformation.
Thereis no debate about the fact that social media platforms have fostered a globalexpression, making the world a global village, bringing everyone together. Onthe other hand, the platforms have become the epicentre of computer-basedcrimes, where children and teenagers often become prey to these crimes,cyberbullying, and cyberstalking.
Rising Importance of Platform Accountability
Themost pertinent question that is to be asked with a conscious mind is whether anunregulated media is a reflection of Freedom of Speech, a right given to us byour constitution under Article. 19(1)(a), or whether free speech is just a garbby big stakeholders, and we are all victims of an impending infodemic andvictims of AI algorithms, because, as per the reports that surfaced during theCovid-19 pandemic, India saw a dramatic 214% rise in false information. Anotherreport by the UNESCO-Ipsos survey revealed that 85% of Indian respondentsencounter online hate speech, with around 64% pointing to social media as aprimary source.
While the focus on platform accountability is critical, it is equally important to recognise that the right to free speech is not absolute. Therefore, users also bear a constitutional responsibility while exercising this right. Free expression in a democratic society must be accompanied by civic digital behaviour, which includes refraining from spreading hate speech, misinformation, or engaging in harmful conduct online. The most recent example of this is the case of Ranveer Gautam Allahabadia vs. UOI (popularly known as “Latent Case”); the court came down heavily on the hosts and makers of the show and made its position crystal clear by stating, “there is nothinglike a fundamental right on platter...the fundamental rights are all followedby a duty...unless those people understand duty, there is no [...] deal withthat kind of elements...if somebody wants to enjoy fundamental rights, thiscountry gives a guarantee to enjoy, but guarantee is with a duty so thatguarantee will involve performing that duty also” .
The Way Forward: CyberPeace Suggests
In order to realise the benefits and derive the true benefits from the rights we are provided, especially the one in discussion, i.e., Freedom of Speech and Expression, the government and the designated intermediaries and regulators have to prepare both roadmaps, one for “Platform Accountability” and one for "User Accountability”, wherein the regulators with a reasonable foresight should conduct Algorithm Risk Audits which is a technique to make algorithms and there effects on content feeds visible. It can be an effective tool and an objective manner to compare how algorithms are automatically pushing different content to different users in an unfair or unbalanced way. As for user accountability, “Digital Literacy” is the way forward, ensuring that social media remains a marketplace of ideas and does not become a minefield of misfires.


